Day 46 of Becoming a SOC Analyst | Follina 0-Day in the Wild — CVE-2022-30190 Phishing to RCE скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Day 46 of Becoming a SOC Analyst | Follina 0-Day in the Wild — CVE-2022-30190 Phishing to RCE в качестве 4k
У нас вы можете посмотреть бесплатно Day 46 of Becoming a SOC Analyst | Follina 0-Day in the Wild — CVE-2022-30190 Phishing to RCE или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Day 46 of Becoming a SOC Analyst | Follina 0-Day in the Wild — CVE-2022-30190 Phishing to RCE в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Day 46 of Becoming a SOC Analyst | Follina 0-Day in the Wild — CVE-2022-30190 Phishing to RCE
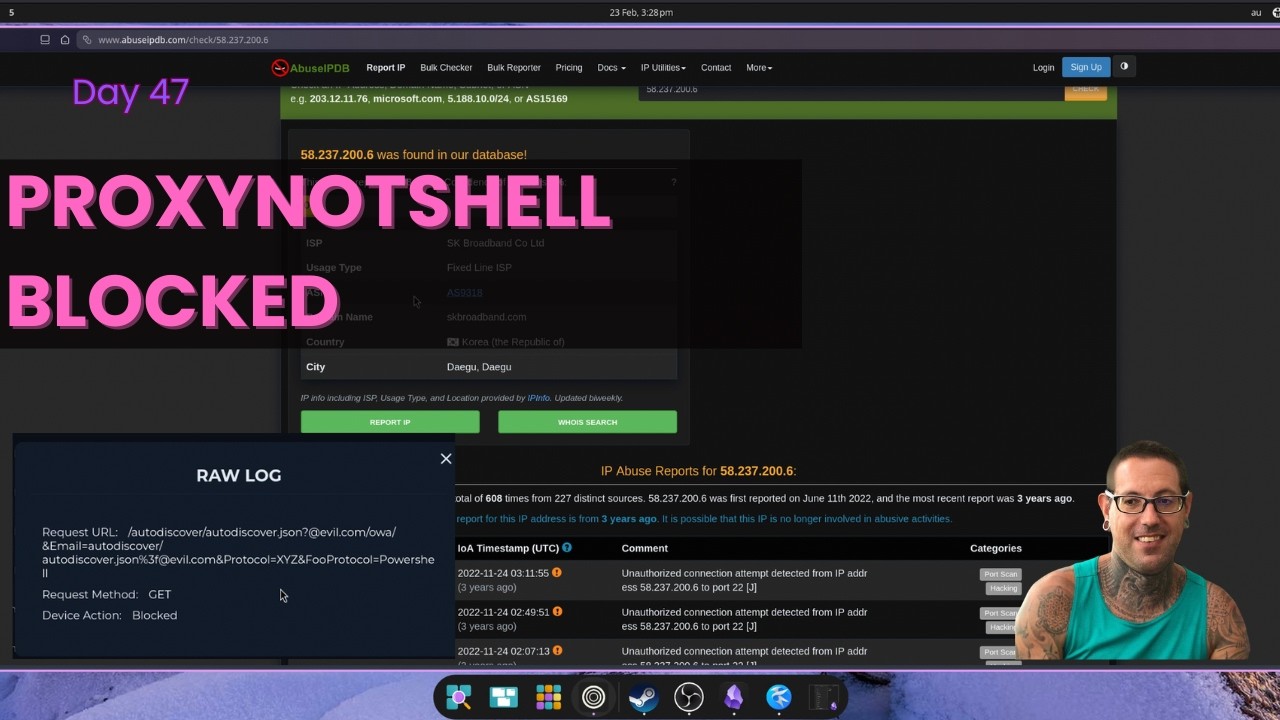
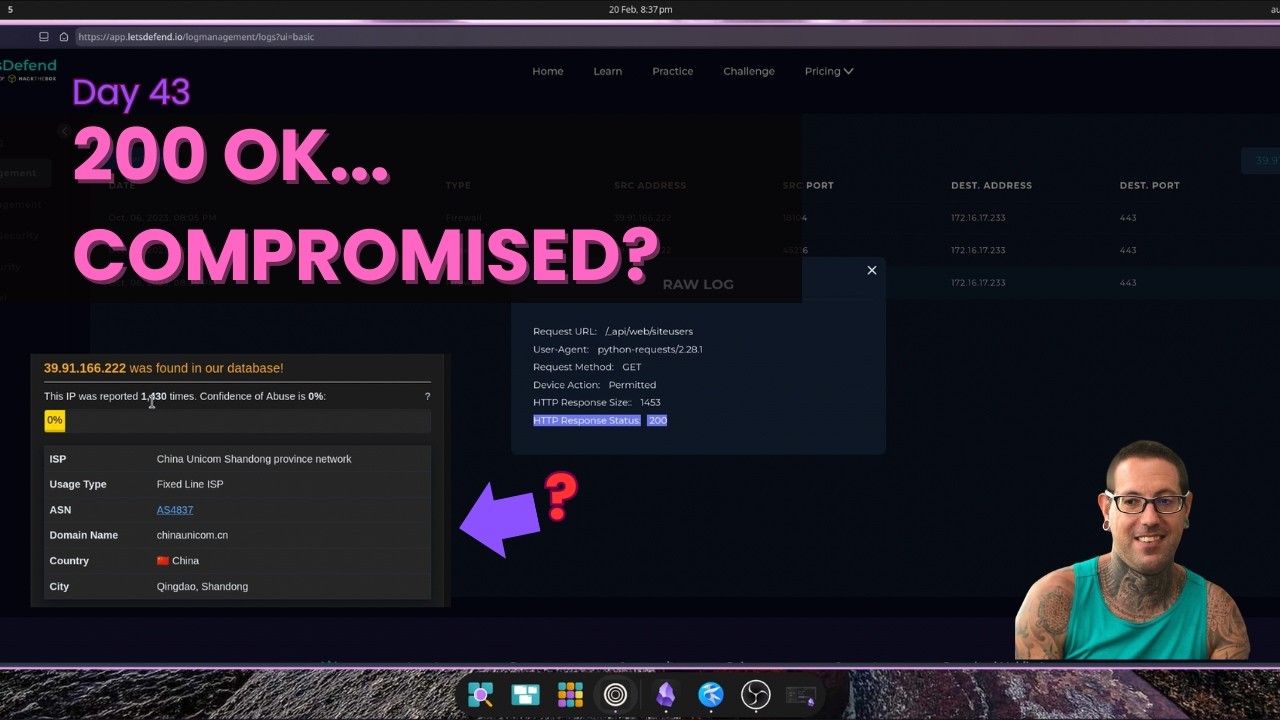
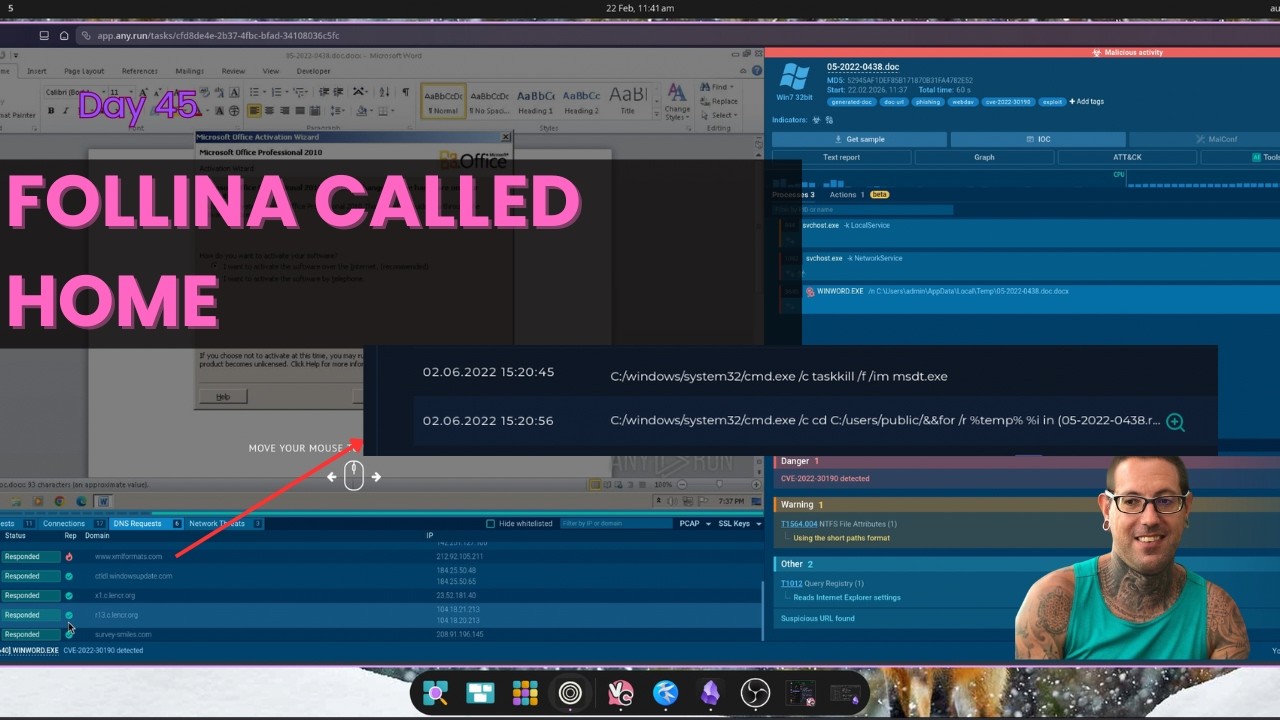
Day 46 of Becoming a SOC Analyst — Follina CVE-2022-30190 / Phishing to RCE via MSDT (True Positive) Malicious email from radiosputnik@ria.ru delivered a password protected ZIP containing a Word doc that exploited the Follina vulnerability. Opening 05-2022-0438.doc abused Microsoft's Windows Support Diagnostic Tool to achieve remote code execution — no macros, no VBA, just msdt.exe spawning off an Office process. HTTP logs and sandbox analysis in any.run confirmed outbound C2 communication to 141.105.65.149. Walked through phishing delivery analysis, MSDT abuse identification, file hash triage, C2 attribution, sandbox confirmation, MITRE mapping (T1204, T1059.003, T1203, T1105, T1218), and full containment — host isolation, artifact removal, IOC blocking. Scenario sourced from LetsDefend.io — one of the best hands-on SOC analyst training platforms out there. Highly recommend if you're on the same path. I'm documenting every day of my journey to landing a Level 1 SOC Analyst role — the wins, the grinds, and everything in between. 🔵 What I Cover Threat Detection · Alert Triage · SIEM Analysis · PCAP Review · Incident Response · Blue Team Tools 🚨 Open to Work — Seeking a Level 1 SOC Analyst role in Melbourne or Remote (AU) 📂 Portfolio → inksec.io 💼 LinkedIn → linkedin.com/in/tate-pannam-8b64b23a3 If you chose the red pill... 0x74617465.sh #SOCAnalyst #BlueTeam #Cybersecurity #Follina #CVE202230190 #MSDT #MalwareAnalysis #IncidentResponse #SIEM #Day46 #CyberSecurityJourney #Melbourne #LetsDefend #LetsDefendSOC #Phishing #ThreatHunting