Analyzing Python Malware скачать в хорошем качестве
malware
exploit
anonymous
metasploit
heapspray
heap
shellcode
spam
virus
trojan
c++
python
java
javascript
html
ollydbg
windbg
idapro
windows
linux
ransomware
script
shell
powershell
backdoor
code
algorithm
analysis
cve
microsoft
adobe
zeroday
0day
mac
kali
cisco
ringzerolabs
alienvault
password
network
CEH
server
client
cryptography
encryption
decryption
android
apk
asmr
reverse engineering
hacking
cyber security
malware analysis
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Analyzing Python Malware в качестве 4k
У нас вы можете посмотреть бесплатно Analyzing Python Malware или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Analyzing Python Malware в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Analyzing Python Malware
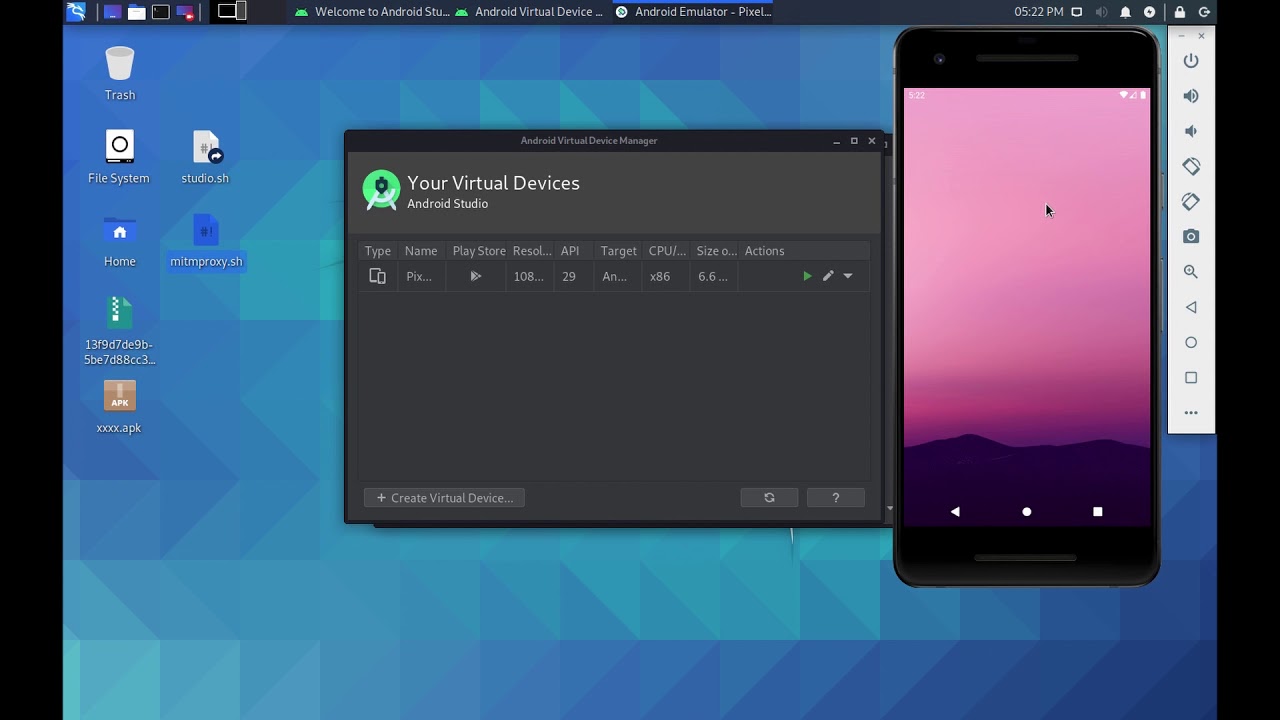
Blog Article For This Video: https://www.RingZeroLabs.com/2020/09/... How do you get started in Malware Analysis? First, you need an analysis environment in-place to investigate files. Here is the fastest way to automatically setup a Virtual Lab Environment complete with a FREE VM directly from Microsoft and FREE analysis tools: http://bit.ly/2Z5LgXa REDDIT: / ringzero TWITTER: / ringzerolabs FACEBOOK: / ring-zero-labs-110227123029488 Ring Ø Labs is a Reverse Engineering site dedicated to analyzing malware, researching emergent security topics, and hacking the planet :) Here are some approaches in reverse engineering a malware sample: Reverse engineer: The most obvious approach is to completely reverse engineer a piece of malware. This obviously takes a great amount of time, so other approaches are more practical. Exploitation techniques: Another approach you can take is to focus on the exploitation techniques of a piece of malware. Occasionally you will see a piece of malware that is using a new exploitation technique, or is exploiting a zero-day vulnerability. In this case you may be interested only in the specific exploitation technique so you can timebox your analysis and only look at the exploitation mechanisms. Obfuscation: Malware will often obfuscate itself and make itself difficult to analyze. You might come across malware that you have seen before without obfuscation. In that case you may only want to focus on reverse engineering the new parts. Encryption methods: A common type of malware these days is ransomware. Ransomware essentially encrypts the victim's files and locks them up so that they can't be accessed or read. Oftentimes the authors of ransomware will make mistakes when they implement the encryption mechanisms. So if you focus your research on the encryption mechanisms you might be able to find weaknesses in their implementation and/or you might be able to find hard-coded keys or weak algorithms. C&C communication: This is something that is pretty commonly done when looking at malware. Analysts often want to figure out what the communication protocol is between a piece of malware on the client's side and the server on the command and control side. The communication protocol can actually give you a lot of hints about the malware’s capabilities. Attribution: Murky area - kind of like a dark art. It usually involves a lot of guesswork, knowledge of malicious hacking teams and looking at more than one piece of malware. Categorization and clustering: You can reverse engineer malware from a broader point of view. This involves looking at malware in bulk and doing a broad-stroke analysis on lots of different malware, rather than doing a deep dive. Techniques Now, let’s look at techniques that can be utilized while analyzing malware. First of all, we use static analysis. This is the process of analyzing malware or binaries without actually running them. It can be as simple as looking at metadata from a file. It can range from doing disassembly or decompilation of malware code to symbolic execution, which is something like virtual execution of a binary without actually executing it in a real environment. Conversely, dynamic analysis is the process of analyzing a piece of malware when you are running it in a live environment. In this case, you are often looking at the behavior of the malware and looking at the side effects of what it is doing. You are running tools like process monitor and sysmon to see what kinds of artifacts a piece of malware produces after it is run. We also use automated analysis. Oftentimes if you are looking at malware you want to automate things just to speed up the process to save time. However, use caution, as with automated analysis sometimes things get missed because you are trying to do things generically. If a piece of malware contains things like anti-debugging routines or anti-analysis mechanisms, you may want to perform a manual analysis. You need to pick the right tools for the job. Happy Hunting :)






![🐍 UNDETECTABLE PYTHON VIRUS EXAMPLE + SOURCE CODE [MALWARE] #make #python #malware #coding](https://imager.clipsaver.ru/QYPYYU8IZzA/max.jpg)