TryHackMe Burp Suite: The Basics | Full Walkthrough 2026 —Å–∫–∞—á–∞—Ç—å –≤ —Ö–æ—Ä–æ—à–µ–º –∫–∞—á–µ—Å—Ç–≤–µ
–ü–æ–≤—Ç–æ—Ä—è–µ–º –ø–æ–ø—ã—Ç–∫—É...
–°–∫–∞—á–∞—Ç—å –≤–∏–¥–µ–æ —Å —é—Ç—É–± –ø–æ —Å—Å—ã–ª–∫–µ –∏–ª–∏ —Å–º–æ—Ç—Ä–µ—Ç—å –±–µ–∑ –±–ª–æ–∫–∏—Ä–æ–≤–æ–∫ –Ω–∞ —Å–∞–π—Ç–µ: TryHackMe Burp Suite: The Basics | Full Walkthrough 2026 –≤ –∫–∞—á–µ—Å—Ç–≤–µ 4k
–£ –Ω–∞—Å –≤—ã –º–æ–∂–µ—Ç–µ –ø–æ—Å–º–æ—Ç—Ä–µ—Ç—å –±–µ—Å–ø–ª–∞—Ç–Ω–æ TryHackMe Burp Suite: The Basics | Full Walkthrough 2026 –∏–ª–∏ —Å–∫–∞—á–∞—Ç—å –≤ –º–∞–∫—Å–∏–º–∞–ª—å–Ω–æ–º –¥–æ—Å—Ç—É–ø–Ω–æ–º –∫–∞—á–µ—Å—Ç–≤–µ, –≤–∏–¥–µ–æ –∫–æ—Ç–æ—Ä–æ–µ –±—ã–ª–æ –∑–∞–≥—Ä—É–∂–µ–Ω–æ –Ω–∞ —é—Ç—É–±. –î–ª—è –∑–∞–≥—Ä—É–∑–∫–∏ –≤—ã–±–µ—Ä–∏—Ç–µ –≤–∞—Ä–∏–∞–Ω—Ç –∏–∑ —Ñ–æ—Ä–º—ã –Ω–∏–∂–µ:
-
–ò–Ω—Ñ–æ—Ä–º–∞—Ü–∏—è –ø–æ –∑–∞–≥—Ä—É–∑–∫–µ:
–°–∫–∞—á–∞—Ç—å mp3 —Å —é—Ç—É–±–∞ –æ—Ç–¥–µ–ª—å–Ω—ã–º —Ñ–∞–π–ª–æ–º. –ë–µ—Å–ø–ª–∞—Ç–Ω—ã–π —Ä–∏–Ω–≥—Ç–æ–Ω TryHackMe Burp Suite: The Basics | Full Walkthrough 2026 –≤ —Ñ–æ—Ä–º–∞—Ç–µ MP3:
–ï—Å–ª–∏ –∫–Ω–æ–ø–∫–∏ —Å–∫–∞—á–∏–≤–∞–Ω–∏—è –Ω–µ
–∑–∞–≥—Ä—É–∑–∏–ª–∏—Å—å
–ù–ê–ñ–ú–ò–¢–ï –ó–î–ï–°–¨ –∏–ª–∏ –æ–±–Ω–æ–≤–∏—Ç–µ —Å—Ç—Ä–∞–Ω–∏—Ü—É
–ï—Å–ª–∏ –≤–æ–∑–Ω–∏–∫–∞—é—Ç –ø—Ä–æ–±–ª–µ–º—ã —Å–æ —Å–∫–∞—á–∏–≤–∞–Ω–∏–µ–º –≤–∏–¥–µ–æ, –ø–æ–∂–∞–ª—É–π—Å—Ç–∞ –Ω–∞–ø–∏—à–∏—Ç–µ –≤ –ø–æ–¥–¥–µ—Ä–∂–∫—É –ø–æ –∞–¥—Ä–µ—Å—É –≤–Ω–∏–∑—É
—Å—Ç—Ä–∞–Ω–∏—Ü—ã.
–°–ø–∞—Å–∏–±–æ –∑–∞ –∏—Å–ø–æ–ª—å–∑–æ–≤–∞–Ω–∏–µ —Å–µ—Ä–≤–∏—Å–∞ ClipSaver.ru
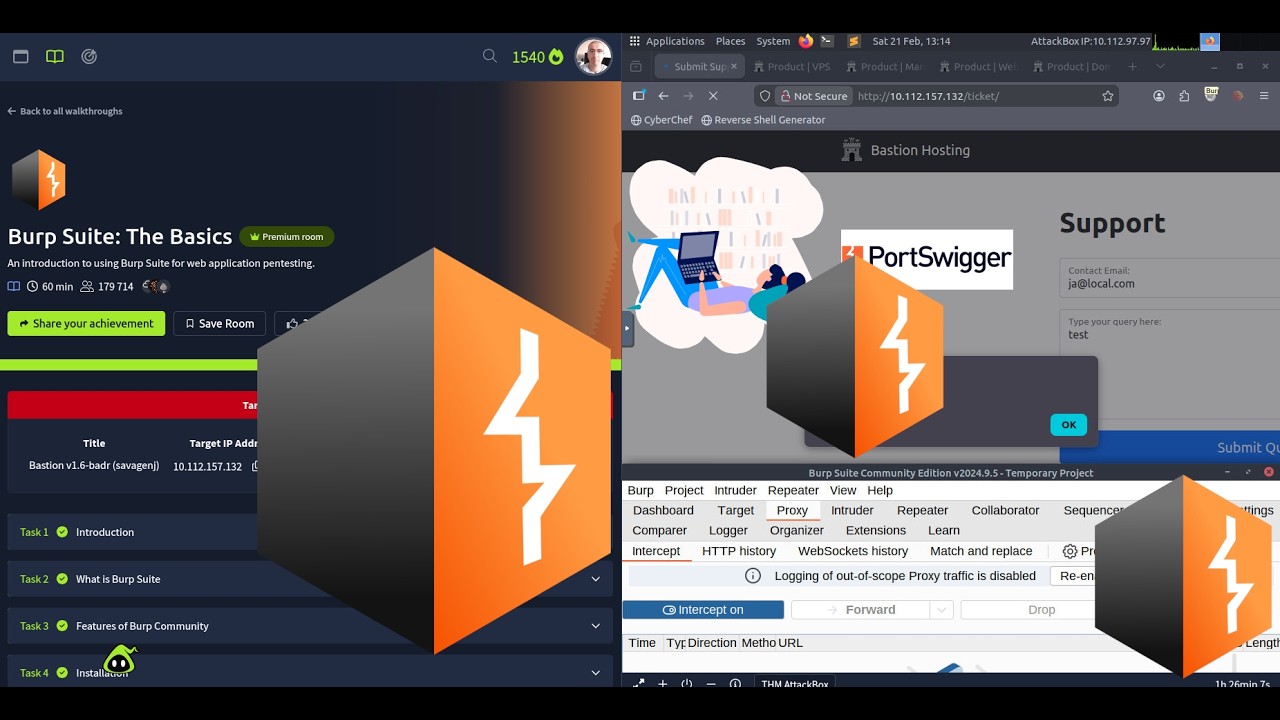
TryHackMe Burp Suite: The Basics | Full Walkthrough 2026
An introduction to using Burp Suite for web application pentesting. üîóüîó Room link: https://tryhackme.com/room/burpsuiteb... üö® Room Tasks: üö® üéê Task 1: Introduction üéê Task 2: What is Burp Suite -Which edition of Burp Suite runs on a server and provides constant scanning for target web apps? Burp Suite is frequently used when attacking web applications and ______ applications. üéê Task 3: Features of Burp Community Which Burp Suite feature allows us to intercept requests between ourselves and the target? Which Burp tool would we use to brute-force a login form? üéê Task 4: Installation üéê Task 5: The Dashboard What menu provides information about the actions performed by Burp Suite, such as starting the proxy, and details about connections made through Burp? üéê Task 6: Navigation Which tab Ctrl + Shift + P will switch us to? üéê Task 7: Options In which category can you find a reference to a "Cookie jar"? In which base category can you find the "Updates" sub-category, which controls the Burp Suite update behaviour? What is the name of the sub-category which allows you to change the keybindings for shortcuts in Burp Suite? If we have uploaded Client-Side TLS certificates, can we override these on a per-project basis (yea/nay)? üéê Task 8: Introduction to the Burp Proxy üéê Task 9: Connecting through the Proxy (FoxyProxy) üéê Task 10: Site Map and Issue Definitions What is the flag you receive after visiting the unusual endpoint? üéê Task 11: The Burp Suite Browser üéê Task 12: Scoping and Targeting üéê Task 13: Proxying HTTPS üéê Task 14: Example Attack üéê Task 15: Conclusion ‚öÝÔ∏è Educational Purpose Only This content is for educational and authorized penetration testing purposes only. Always ensure you have permission before testing on any systems. #tryhackme















![–í–∫–ª—é—á–∞–µ–º —Å–µ–∫—Ä–µ—Ç–Ω—ã–π –ø—Ä–æ—Ç–æ–∫–æ–ª MTproxy –¥–ª—è Telegram –ø—Ä–æ—Ç–∏–≤ –∑–∞–º–µ–¥–ª–µ–Ω–∏–π. [goTelegram —Å–∫—Ä–∏–ø—Ç]](https://imager.clipsaver.ru/3O7iigCHd8U/max.jpg)


