How to Bypass VMProtect & Remove Virtualization | Complete Deobfuscation & Devirtualization Program скачать в хорошем качестве
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: How to Bypass VMProtect & Remove Virtualization | Complete Deobfuscation & Devirtualization Program в качестве 4k
У нас вы можете посмотреть бесплатно How to Bypass VMProtect & Remove Virtualization | Complete Deobfuscation & Devirtualization Program или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон How to Bypass VMProtect & Remove Virtualization | Complete Deobfuscation & Devirtualization Program в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
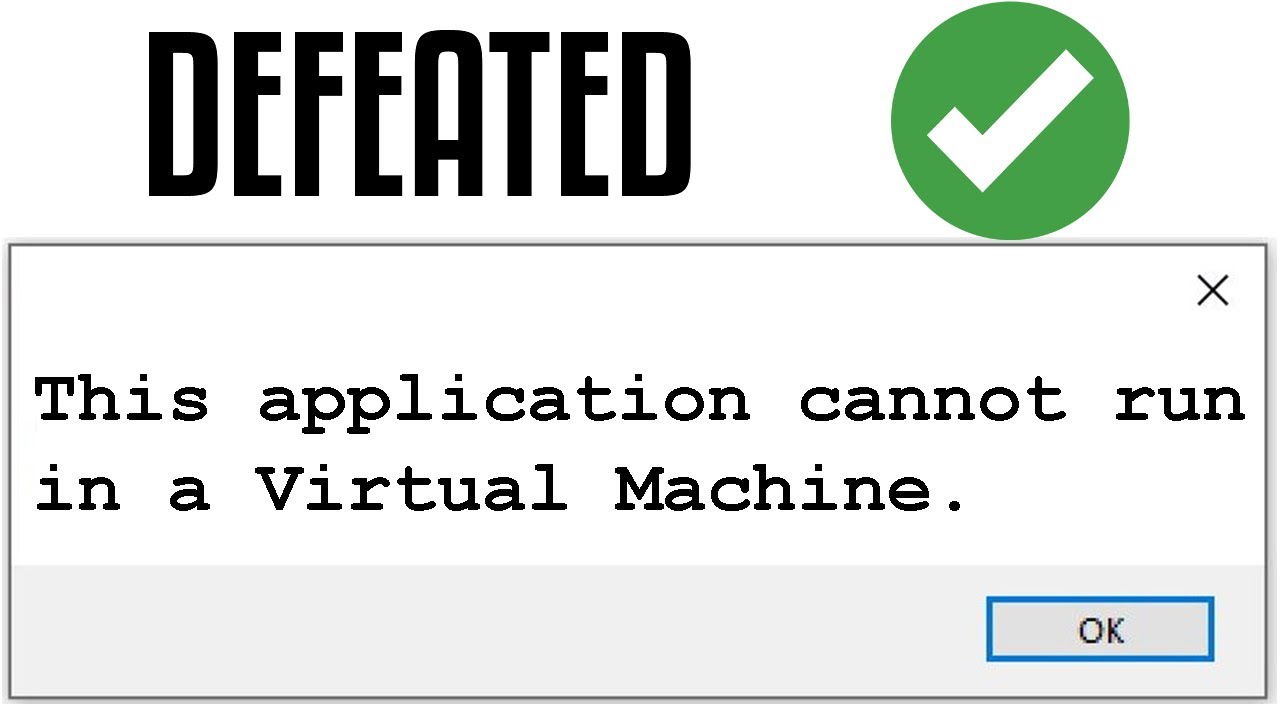
How to Bypass VMProtect & Remove Virtualization | Complete Deobfuscation & Devirtualization Program
》 Telegram : t.me/reverseengineerr 💡 Want to analyze, deobfuscate, and devirtualize a VMProtect-protected DLL or EXE? You’re in the right place! VMProtect is one of the most advanced software protection tools, but with the right approach, its virtualization, control flow obfuscation, and anti-debugging mechanisms can be bypassed! 🎯 What You’ll See in This Video: ✅ Scanning the protected DLL in DIE (Detect It Easy) to confirm VMProtect protection. ✅ Full deobfuscation and devirtualization process (real-time, ~17-18 minutes). ✅ Removing obfuscation, virtualization, anti-debugging, and anti-tampering mechanisms. ✅ Exporting Decompiled Assembly (ASM) & LLVM IR code for further analysis. ✅ Final verification in DIE to confirm VMProtect removal. 🔍 Key Features of VMProtect Analyzer Professional: ✔️ VMProtect 2.X & 3.X Virtualization Bypass ✔️ Control Flow Flattening & Stack Virtualization Removal ✔️ Dynamic Anti-Debug & Anti-Tamper Patching ✔️ Memory Protection Analysis & VM Handler Pattern Recognition ✔️ Decompiling to LLVM IR & Assembly for further inspection 💾 More About VMProtect Analyzer Professional If you're looking for a way to analyze and remove VMProtect’s virtualization & obfuscation to recover readable code, this tool is for you! 📥 Contact & Support: 📧Telegram : t.me/reverseengineerr VMProtect, VMProtect bypass, VMProtect devirtualization, remove VMProtect, VMProtect crack, VMProtect unpack, deobfuscation, anti-debug bypass, software protection, VMProtect analysis, reverse engineering, remove virtualization, VM handler analysis, control flow obfuscation, anti-tamper patch, dynamic deobfuscation, LLVM IR export, decompiled assembly, DLL analysis, EXE deobfuscation, security research, malware analysis, binary analysis, VMProtect 3.X bypass, anti-debug removal, code virtualization, VMProtect unpacking, protectors bypass, security tools, reverse engineering tutorial