(Podcast) Mail2Shell Zero Click Exploit Hijacks FreeScout Servers скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: (Podcast) Mail2Shell Zero Click Exploit Hijacks FreeScout Servers в качестве 4k
У нас вы можете посмотреть бесплатно (Podcast) Mail2Shell Zero Click Exploit Hijacks FreeScout Servers или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон (Podcast) Mail2Shell Zero Click Exploit Hijacks FreeScout Servers в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
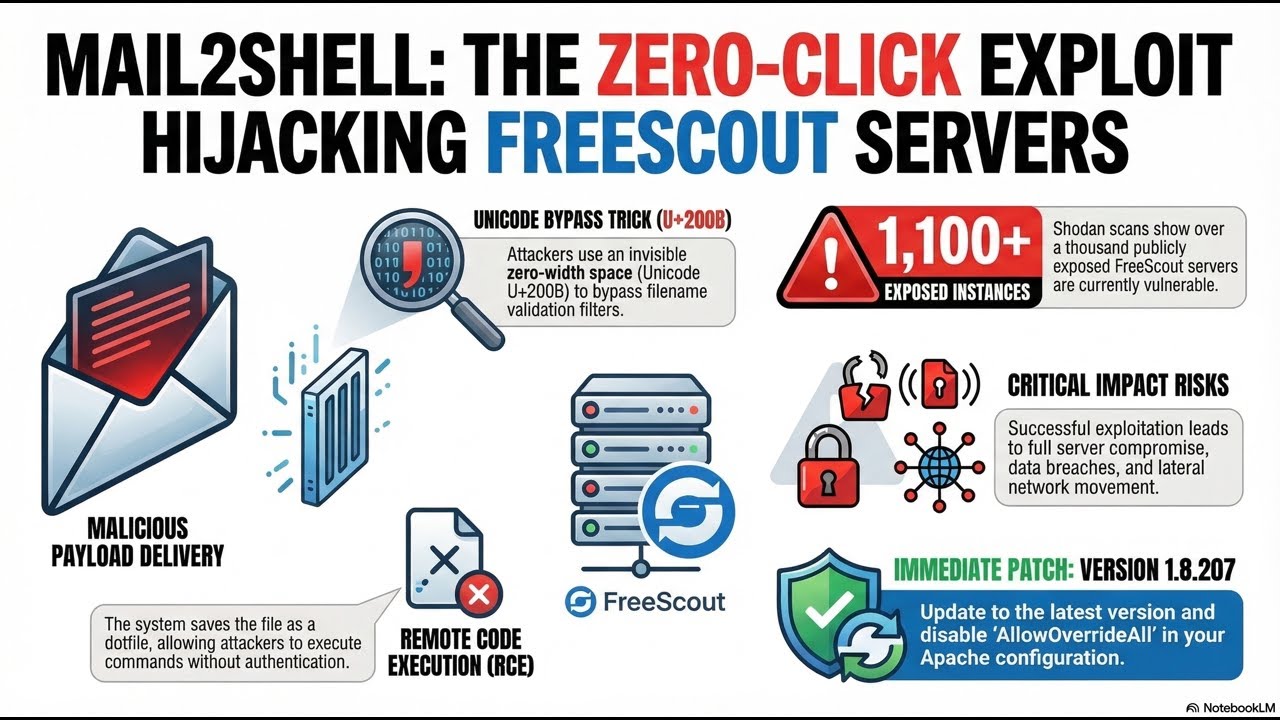
(Podcast) Mail2Shell Zero Click Exploit Hijacks FreeScout Servers
Hey Techies! 🎧 Get ready for a wild ride into the world of "invisible" hacks! In today’s episode, we’re breaking down the Mail2Shell attack—a maximum severity vulnerability tracked as CVE-2026-28289 that allows hackers to achieve remote code execution on FreeScout helpdesk platforms1. This zero-click flaw is a total game-changer because it requires absolutely zero user interaction or authentication to succeed1. Imagine a hack so sneaky it uses a "zero-width space" (a character you can't even see!) to trick security filters and bypass previous fixes2. By sending just one crafted email to a FreeScout address, attackers can stash malicious payloads directly on the server13. Because the platform automatically stores these attachments, hackers can access them through the web interface to execute commands and take total control3. 📧💥 With over 1,100 FreeScout instances currently exposed to the public internet, the stakes couldn't be higher4. We discuss the nightmare scenarios of full server compromise, data breaches, and hackers moving laterally through your internal network5. But don't panic—we’ve got the fix! Learn why you need to update to version 1.8.207 immediately and why disabling 'AllowOverrideAll' in your Apache config is a non-negotiable step for safety45. Tune in to stay protected! 🛡️✨ Source: "Mail2Shell zero-click attack lets hackers hijack FreeScout mail servers" by Bill Toulas, BleepingComputer. #CyberSecurity #FreeScout #ZeroClick #Mail2Shell #Podcast #Infosec #Hacking #RCE #TechNews #ServerSecurity #DataBreach #PatchNow