#Hacktivity2022 скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: #Hacktivity2022 в качестве 4k
У нас вы можете посмотреть бесплатно #Hacktivity2022 или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон #Hacktivity2022 в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
#Hacktivity2022
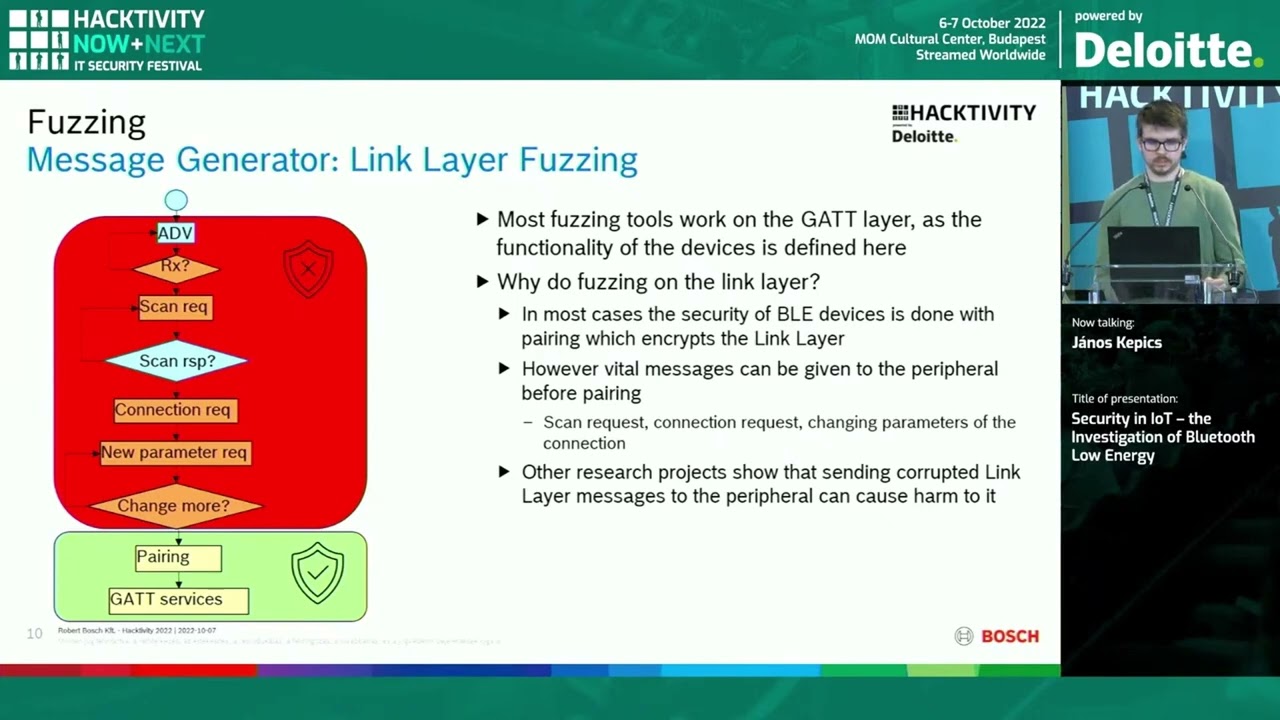
Consumer IoT devices manifest in a variety of forms today, including fitness trackers, rings, smart-watches, pacemakers, and so on. Most short range, low power consuming IoT devices use BLE (Bluetooth Low Energy) protocol to communicate with a master device. This communication link can contain very personal information about the user. Several vulnerabilities and security attacks exist for BLE (Eavesdropping, Man in the Middle Attacks, Denial of Service & Fuzzing Attack). However, most of them do not go down to the lower layers of the protocol (L2CAP, link layer, Physical layer). In my presentation I deep dive into the structure of BLE protocol, explore some of the open-source tools for BLE exploitation (gatttool, bettercap, Ubertooth etc.) and introduce you to the world of software defined radio – how you can use it to analyse and potentially malform packets in the lowest layers of the protocol. https://www.hacktivity.com