WHY 2025 - Using deployment diagrams to explain architecture and security to everybody скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: WHY 2025 - Using deployment diagrams to explain architecture and security to everybody в качестве 4k
У нас вы можете посмотреть бесплатно WHY 2025 - Using deployment diagrams to explain architecture and security to everybody или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон WHY 2025 - Using deployment diagrams to explain architecture and security to everybody в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
WHY 2025 - Using deployment diagrams to explain architecture and security to everybody
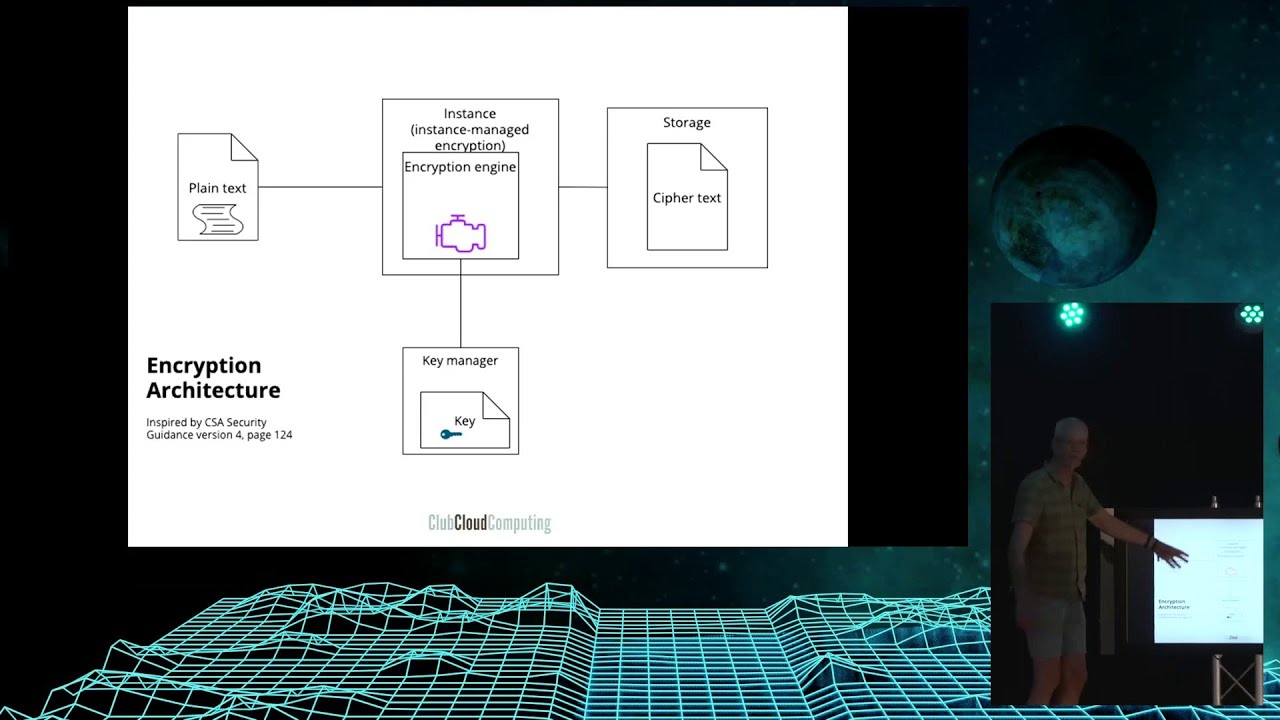
https://media.ccc.de/v/why2025-211-us... This talk will enable you to lead architecture conversations and discuss their security options through an informal diagramming technique. I will use examples such as key/encryption architectures, DevOps, and even your home music system. Presentation at https://digitalinfrastructures.nl/why... You have seen many diagrams of computer and information systems in your career. They have been around since the early days of computing. They can be useful, but there are a few typical problems with them: • They are drawn with obscure symbols that are only understood by architects • They are drawn in an inconsistent way • They are not used to their fullest potential. In my practice I have run into these problems often, and I have found ways to turn a certain type of diagram, a simplified version of deployment diagrams, into the cornerstone of explanation of what goes on in cloud and cybersecurity. In the talk I will lead you through the basic principles, and a few examples. This will enable you to lead architecture conversations and discuss their security options. I will use examples such as key/encryption architectures, DevOps, and even your home music system. Peter van Eijk https://program.why2025.org/why2025/t... #why2025 #Wonderfulcreations Licensed to the public under https://creativecommons.org/licenses/...