In the Trenches: Platform SSO, Okta, Connect, and Network Relay at Jamf скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: In the Trenches: Platform SSO, Okta, Connect, and Network Relay at Jamf в качестве 4k
У нас вы можете посмотреть бесплатно In the Trenches: Platform SSO, Okta, Connect, and Network Relay at Jamf или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон In the Trenches: Platform SSO, Okta, Connect, and Network Relay at Jamf в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
In the Trenches: Platform SSO, Okta, Connect, and Network Relay at Jamf
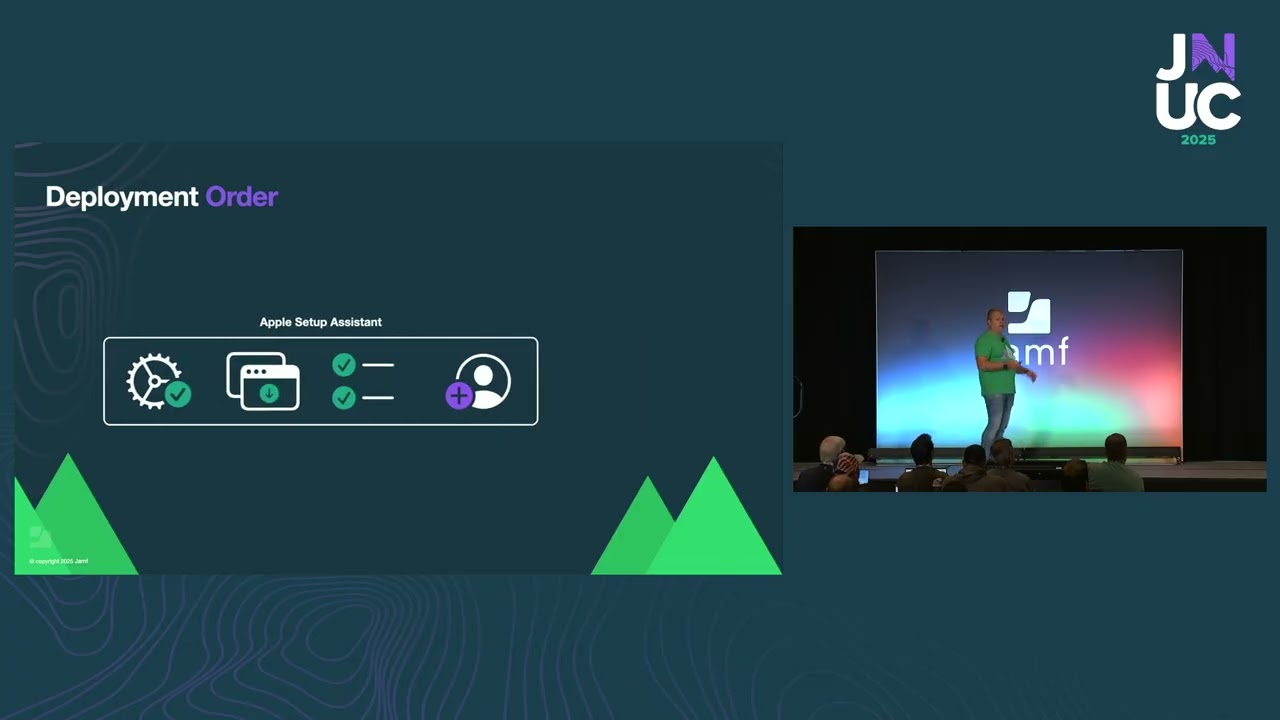
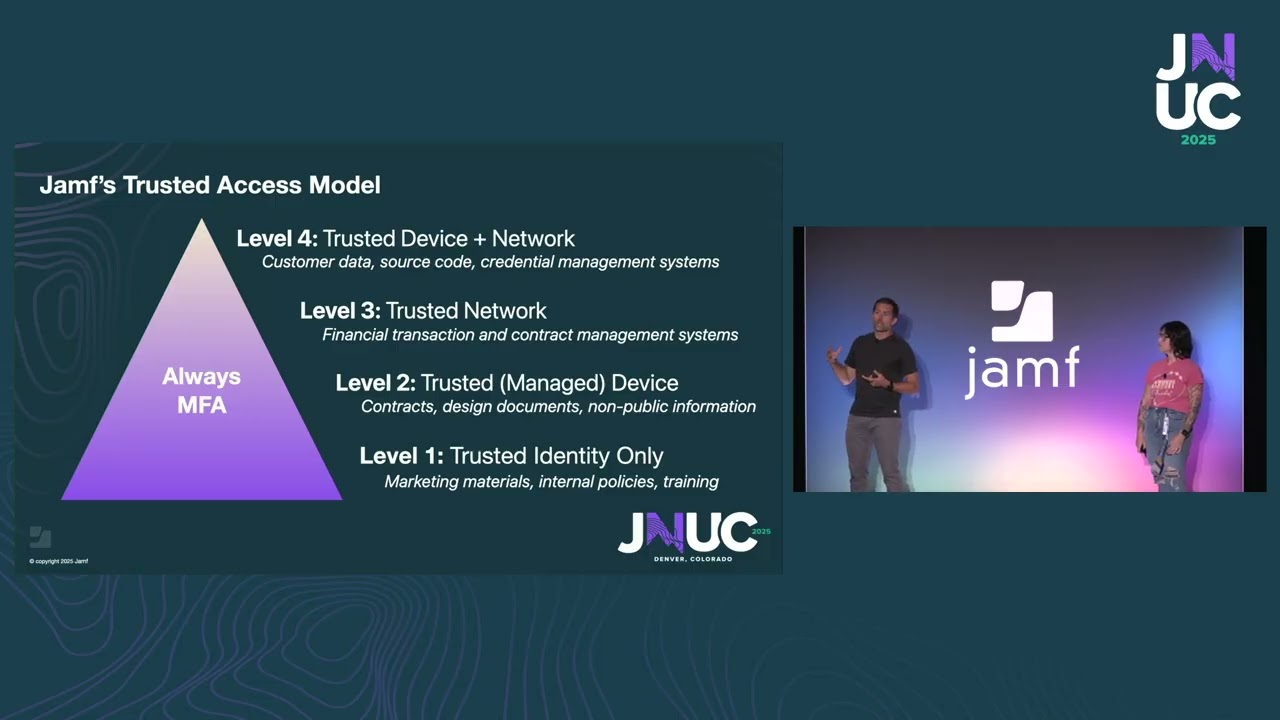
Go field-by-field through Jamf's internal deployment of Platform SSO simplified setup, Network Relay, and managed device attestation. Dr. Emily Kausalik (Manager, Client Platform Engineering) and Matt Vlasach (VP, Product & Solutions Engineering) reveal how Jamf IT manages 2,000+ employees using Jamf Pro, Protect, Security Cloud, Self Service Plus, and Connect, demonstrating real production configurations for Okta Verify FastPass, ACME certificate automation via SmallStep, and zero-touch network access combining WireGuard agent replacement with agentless Network Relay built into macOS 26. See live Jamf Pro console walkthrough showing pre-stage enrollment with simplified setup enabled, single sign-on extension profile with Okta redirect URLs and attribute mappings, SCEP certificate configuration for device access trust layer, and Network Relay activation profile generating ACME and relay payloads. Learn Jamf's four-tier trusted access model requiring managed devices, biometric authentication, and trusted network routing for accessing critical resources like GitHub and Jamf Pro, with conditional access enforcement blocking non-compliant devices until OS updates complete. What You'll Learn: ► Jamf at Jamf internal stack: Pro, Protect, Security Cloud, Self Service Plus, Connect, Okta Verify FastPass ► Four-tier trusted access model: MFA only (level 1), managed device (level 2), trusted network (level 3), all requirements (level 4) ► Platform SSO simplified setup: registration during Setup Assistant creating just-in-time user accounts with Okta attributes ► Okta Verify FastPass: fishing-resistant biometric authentication with Touch ID replacing password entry ► Network Relay agentless access: replacing Jamf Trust WireGuard agent with built-in OS-level VPN ► ACME device attestation PKI: SmallStep integration for Wi-Fi certificates and GitHub SSH key authentication ► User channel MDM enrollment: re-triggering enrollment with sudo profiles renew after user registration for Safari extension management ► Authenticated guest mode vision: tap-to-login with digital employee badges for ephemeral kiosk sessions ► Okta configuration: adding Platform SSO for macOS app, profile editor attribute mapping, SCEP CA setup for device access 0:00 Introduction: Jamf at Jamf Internal Technology Stack 2:03 Device Management: Apple Business Manager, Enrollment Customization, MFA, Jamf Connect Login 5:37 Biometric App Access: Okta Verify FastPass with Touch ID for Jamf Pro Login 7:07 Current ZTNA: Jamf Trust Agent with WireGuard Tunnels and IPsec Site-to-Site VPN 9:27 Managed vs. Unmanaged Devices: Identity-Based Provisioning for Personal Devices 14:04 Conditional Access Blocking: Non-Compliant Device Lockout Until OS Updates 15:11 Next-Gen Automation 2.0: Platform SSO, Network Relay, ACME PKI Integration 16:34 Platform SSO Simplified Setup: Registration During Setup Assistant with Okta Attributes 19:44 Network Relay Agentless Access: Replacing Jamf Trust Agent with OS-Level VPN 21:43 Architecture Comparison: Adding Network Relay to Current Jamf Trust WireGuard Stack 24:19 ACME Device Attestation PKI: SmallStep for Wi-Fi Certificates and GitHub SSH 27:41 Live Demo: Zero-Touch Enrollment with Platform SSO and Network Relay 32:05 Jamf Pro Configuration Walkthrough: Pre-Stage, SSO Extension, SCEP Profile 36:47 Okta Configuration: Adding Platform SSO App, Profile Editor Attribute Mapping 42:05 SCEP Certificate Setup: Device Access CA with Dynamic Provisioning 46:47 Okta Preview Tenant Screenshots: Client ID, Attribute Mapping, Device Access Integration 52:22 Q&A: Authenticated Guest Mode, Password Changes, Admin vs. Standard Accounts 1:00:47 Migration Workflow: Connect to Platform SSO with User Registration and Profiles Renew 1:04:36 Safari Extension Deployment: Why User Channel MDM Matters for Declarative Management #platformSSO #JamfConnect #NetworkRelay #Okta #FastPass #ACME #zerotouchdeployment #zeroTrust #MDM #declarativemanagement Who This Video Is For: Jamf administrators deploying Platform SSO with Okta or Microsoft Entra ID IT teams migrating from Jamf Connect login to simplified setup workflows Organizations implementing Zero Trust frameworks with device attestation Mac admins seeking production-ready configuration examples for Platform SSO Teams evaluating Network Relay for agentless VPN replacement Key Technologies Covered: Platform Single Sign-On (SSO), Jamf Connect, Okta Verify FastPass, Network Relay, ACME device attestation, SmallStep CA, managed device attestation, SCEP certificates, user channel MDM, declarative device management (DDM), Setup Manager, Self Service Plus Related Topics: Zero Trust architecture, fishing-resistant credentials, passwordless authentication, agentless VPN, device identity cryptography, user account lifecycle management, Safari extension deployment, authenticated guest mode, attribute mapping identity providers