Disassembling/Reverse Engineering Course:Branch example 2 скачать в хорошем качестве
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Disassembling/Reverse Engineering Course:Branch example 2 в качестве 4k
У нас вы можете посмотреть бесплатно Disassembling/Reverse Engineering Course:Branch example 2 или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Disassembling/Reverse Engineering Course:Branch example 2 в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Disassembling/Reverse Engineering Course:Branch example 2
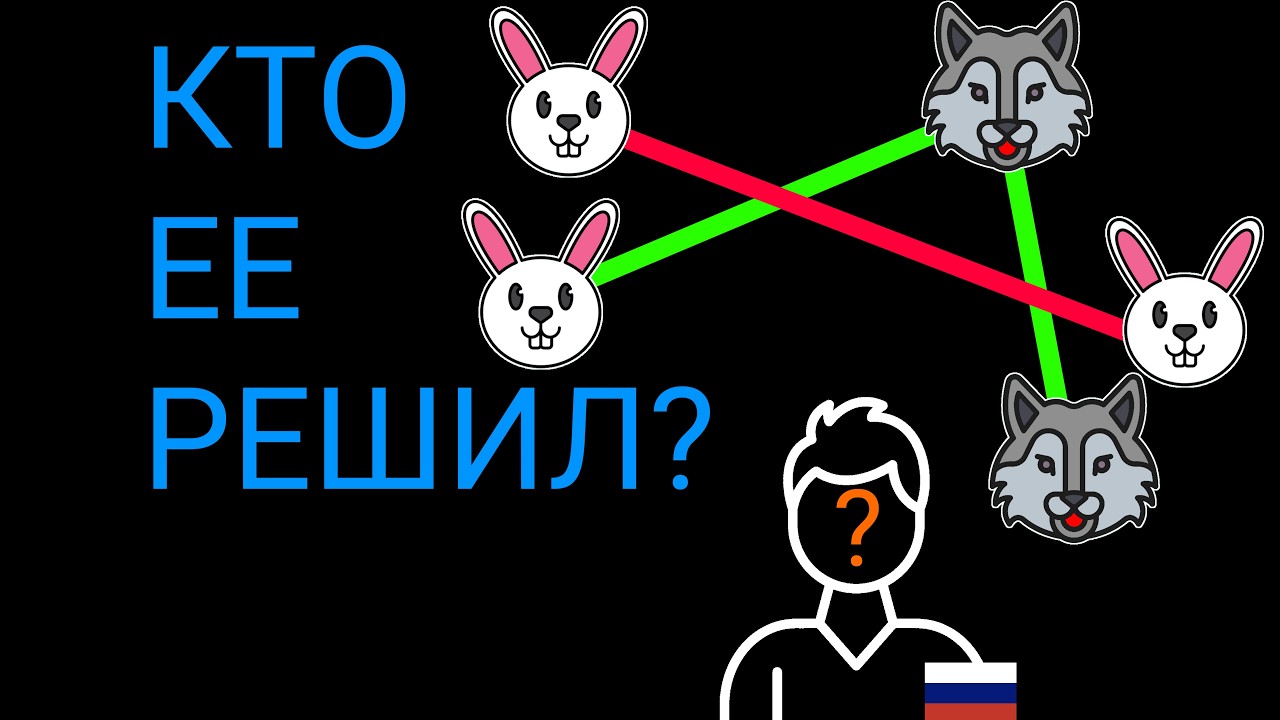
In this lesson, we continue with Branch Example 2, building on previous branch concepts and analyzing a slightly more complex control-flow scenario in disassembled code. Using real assembly examples, we follow execution paths, examine conditional jumps, and see how multiple branches interact to form program logic. This lesson helps sharpen your ability to trace execution accurately when reversing real-world binaries. 🎯 Who this lesson is for: Learners strengthening control-flow analysis skills Students studying assembly and low-level programming Cybersecurity and malware analysis enthusiasts Anyone practicing branch tracing in disassembly Basic familiarity with branch instructions is recommended. By working through this second example, you’ll become more confident reading and understanding complex branching behavior during reverse engineering. 👍 Like the video, 💬 ask questions in the comments, and 🔔 subscribe for more branch examples! #ReverseEngineering #Disassembling #Assembly #Branches #ControlFlow #BinaryAnalysis #CyberSecurity