Fileless скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Fileless в качестве 4k
У нас вы можете посмотреть бесплатно Fileless или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Fileless в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Fileless
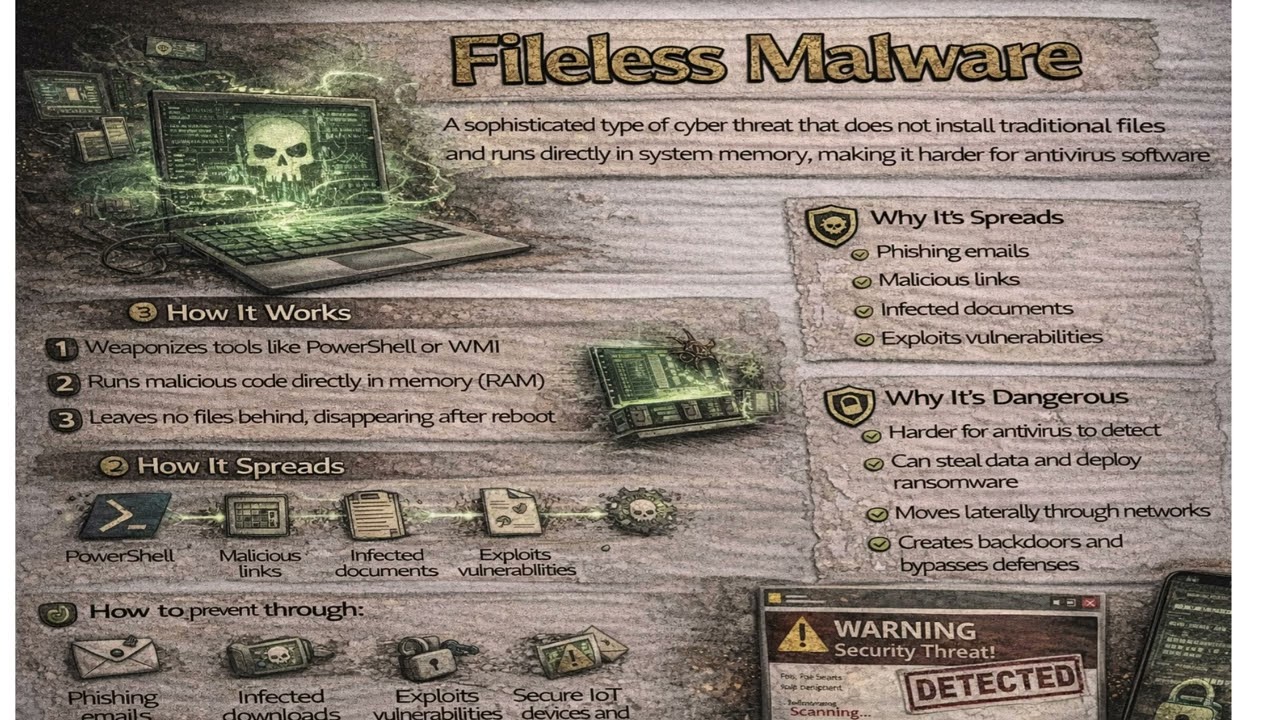
Fileless Malware is a sophisticated type of cyber threat that does not install traditional files on a computer’s hard drive. Instead of leaving detectable files behind like typical viruses or trojans, it operates directly in the system’s memory (RAM). Because it does not rely on stored executable files, it is much harder for traditional antivirus software to detect. Fileless malware often exploits legitimate system tools such as PowerShell, Windows Management Instrumentation (WMI), or other built-in administrative utilities to carry out malicious activities. It usually enters a system through phishing emails, malicious links, infected documents, or by exploiting software vulnerabilities. Once executed, it runs in memory and may disappear after a system reboot—although some advanced versions can maintain persistence. Since it operates in memory and uses trusted system processes, fileless malware can bypass signature-based security solutions. This makes it particularly dangerous for organizations, as it can steal sensitive data, move laterally across networks, deploy ransomware, or create backdoors without triggering obvious alerts. To protect against fileless malware, users and organizations should keep systems updated, disable unnecessary scripting tools, use advanced endpoint detection and response (EDR) solutions, enable behavior-based monitoring, implement strong email security filters, and train employees to recognize phishing attempts.



















