Why Every Hacker Needs to Know the "4-2-1" Rule скачать в хорошем качестве
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Why Every Hacker Needs to Know the "4-2-1" Rule в качестве 4k
У нас вы можете посмотреть бесплатно Why Every Hacker Needs to Know the "4-2-1" Rule или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Why Every Hacker Needs to Know the "4-2-1" Rule в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
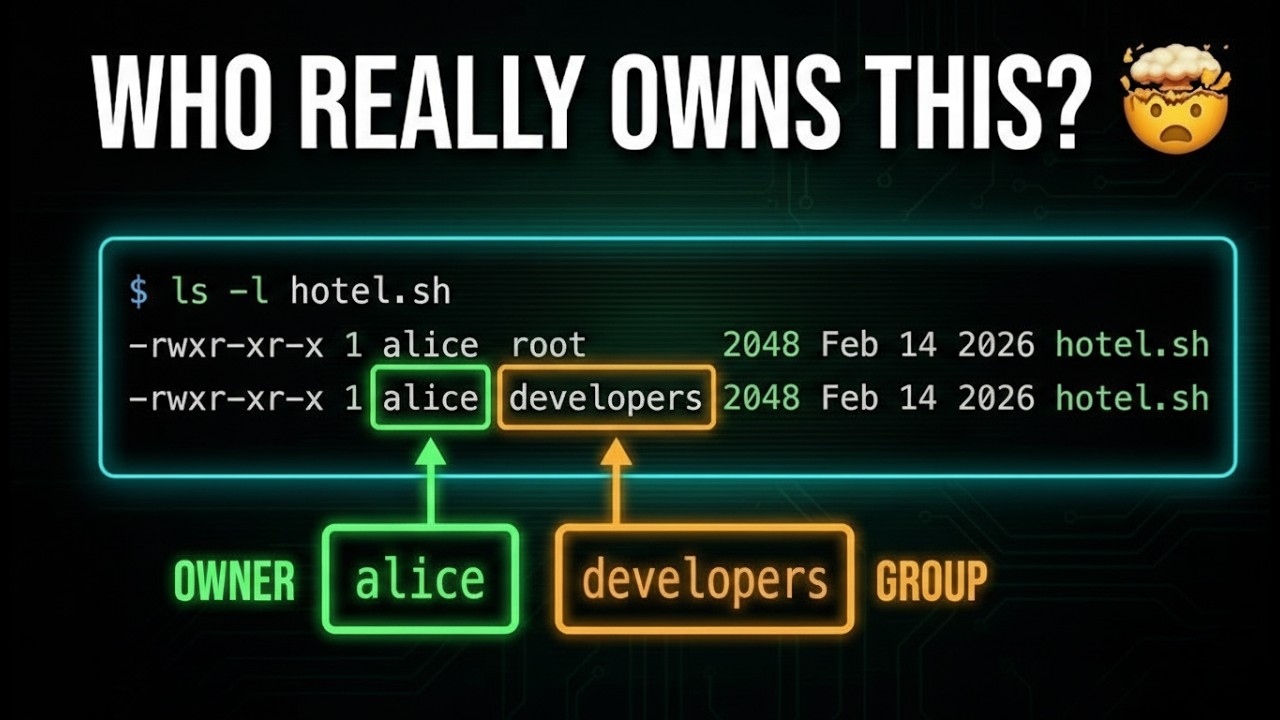
Why Every Hacker Needs to Know the "4-2-1" Rule
In this step-by-step tutorial, I'll show you the easiest and fastest way to master Linux Octal Notation—no more guessing what numbers like 755 or 644 mean! Learn how to calculate Linux permissions using the simple "Hotel Manager" method. This complete Linux file permissions tutorial shows you how to use the chmod command with numbers instead of letters. Perfect for beginners who are learning Linux basics, preparing for a cybersecurity career, or starting their Privilege Escalation journey in Kali Linux. This step-by-step Linux security guide walks you through the 4-2-1 rule, showing you exactly how to convert symbolic permissions (rwx) into octal codes (777). You'll learn how to modify file access, understand owner vs. group permissions, and identify "dangerous" settings that could leave your system vulnerable. Whether you're learning ethical hacking, studying for the CompTIA Linux+ or OSCP, preparing for penetration testing, or just want to manage your Ubuntu or Kali Linux server like a pro—this tutorial shows you the "hacker's shortcut" to mastering the Linux command line. 🎓 Prerequisites: Any Linux distribution (Kali Linux, Ubuntu, Debian, etc.) Basic understanding of the Terminal / Command Line A "Read, Write, Execute" mindset 5 minutes of your time! ⚠️ Important Notes: Octal notation is the industry standard for Linux SysAdmins Using 777 permissions is high-risk and usually unnecessary The chmod command is your primary tool for these changes Understanding these numbers is KEY for Linux Privilege Escalation Calculations are done in "blocks" of three (User, Group, Others) 🔧 The 4-2-1 Rule Breakdown: Read (r): 4 Write (w): 2 Execute (x): 1 No Permission (-): 0 TIMESTAMPS: 0:00 - Intro 0:00 - The "Hotel Manager" Analogy 0:00 - Why Numbers are Faster than Letters 0:00 - The 4-2-1 Value Secret 0:00 - Hands-on chmod Examples in Kali Linux 0:000 - How to Calculate Octal in Your Head 0:00 - Converting Symbolic to Octal (Step-by-Step) 8:44 - Practice & Final Tips Looking for how to understand linux permissions? Need a complete linux octal notation tutorial that's beginner-friendly? Wondering how to use chmod with numbers or searching for linux file security guides? This video covers everything about octal vs symbolic notation and shows you the easiest way to manage linux privileges without complications. Whether you're searching for a linux permission setup guide, wondering how to calculate chmod 755 properly, looking for linux for beginners tutorials, or trying to understand rwx permissions—this complete walkthrough has you covered. Learn the linux command line tutorial method with step-by-step linux file system guidance. Curious about how to use kali linux permissions, where to find the chmod command, or how linux user groups work? Need help with linux privilege escalation basics or want to secure your linux files safely? This tutorial provides a linux complete guide for ethical hacking setup and penetration testing security fundamentals. Find out how to change permissions in linux, get your file access right, follow a beginner linux security tutorial, identify weak permissions properly, and create your cybersecurity lab setup on kali linux or ubuntu. Includes terminal tutorial basics, file system for hacking configuration, solutions for common chmod problems, and complete linux permissions setup instructions.