🚀 Rate Limiting Vulnerabilities | How to Exploit & Secure APIs! | DevAcademix Cybersecurity скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: 🚀 Rate Limiting Vulnerabilities | How to Exploit & Secure APIs! | DevAcademix Cybersecurity в качестве 4k
У нас вы можете посмотреть бесплатно 🚀 Rate Limiting Vulnerabilities | How to Exploit & Secure APIs! | DevAcademix Cybersecurity или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон 🚀 Rate Limiting Vulnerabilities | How to Exploit & Secure APIs! | DevAcademix Cybersecurity в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
🚀 Rate Limiting Vulnerabilities | How to Exploit & Secure APIs! | DevAcademix Cybersecurity
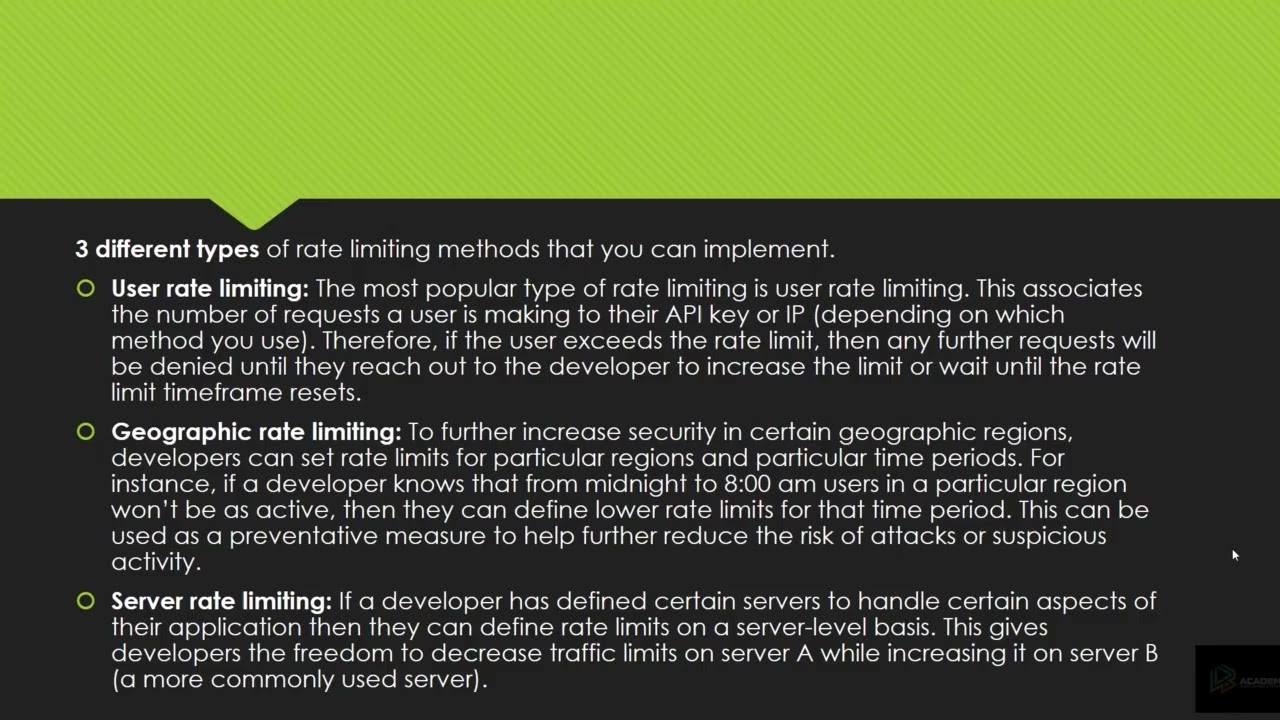
🚀 Welcome to DevAcademix – Your Ultimate Cybersecurity Learning Hub! 🔐 🔍 Exploiting Rate Limiting Vulnerabilities for Bug Bounty Hunting! Rate limiting is a crucial security mechanism to prevent brute-force attacks, API abuse, and DoS attacks. However, misconfigurations can allow attackers to bypass restrictions, leading to account takeovers, data scraping, and credential stuffing attacks. In this video, we’ll demonstrate rate limit bypass techniques, explore real-world bug bounty cases, and discuss mitigation strategies. 💡 Why Watch This Video? ✅ Hands-on exploitation of rate limiting flaws ✅ Understand how attackers bypass security mechanisms ✅ Learn API & web application security best practices ✅ Real-world bug bounty case studies 📌 Subscribe Now & Turn on 🔔 Notifications for weekly cybersecurity content! 🌍 Learn More with DevAcademix: 🌐 Website: https://www.devacademix.com 📚 Bug Bounty Course: https://www.devacademix.com/course 📩 Contact Us: vishal@devacademix.com 🚀 Follow Us for More Updates: 🔗 LinkedIn: https://www.linkedin.com/company/devacademix/ 📢 Subscribe & Hit the Bell Icon 🔔 for more cybersecurity tutorials, ethical hacking tips, and bug bounty guidance! 💬 Have questions? Drop a comment below! 🚀 #RateLimit #BugBounty #EthicalHacking #CyberSecurity #WebSecurity #PenetrationTesting #BurpSuite #APIHacking #BruteForce #DevAcademix #DevAcademix #CyberSecurity #EthicalHacking #BugBounty #DigitalForensics #DevAcademix #DevAcademixCyberSecurity #CyberSecurityWithDevAcademix #LearnWithDevAcademix #DevAcademixTraining #DevAcademixAcademy #DevAcademixYT Cybersecurity-Specific Tags: #DevAcademixCyber #CyberSecByDevAcademix #EthicalHackingWithDevAcademix #DevAcademixBugBounty #DevAcademixForensics #DevAcademixPentest #MalwareAnalysisDevAcademix



















