What are Ports in Computer Networking? | TCP/UDP, Multiplexing & Sockets Explained скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: What are Ports in Computer Networking? | TCP/UDP, Multiplexing & Sockets Explained в качестве 4k
У нас вы можете посмотреть бесплатно What are Ports in Computer Networking? | TCP/UDP, Multiplexing & Sockets Explained или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон What are Ports in Computer Networking? | TCP/UDP, Multiplexing & Sockets Explained в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
What are Ports in Computer Networking? | TCP/UDP, Multiplexing & Sockets Explained
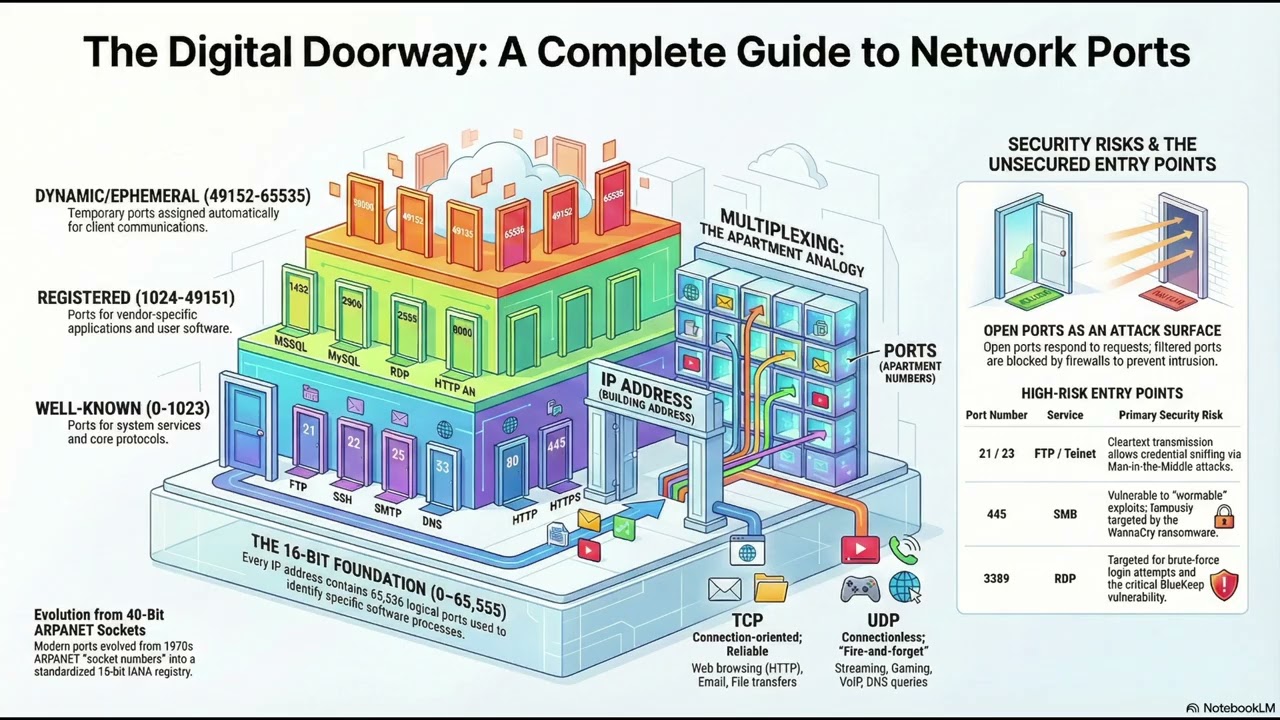
Ever wonder how your computer manages multiple web browser tabs, an email client, and a multiplayer game all over a single internet connection? It is all thanks to Network Ports! In this video, we break down everything you need to know about ports in computer networking, from the basics of TCP and UDP to advanced concepts like the "5-Tuple" and port scanning. Whether you are studying for your CCNA, Network+, or just want to understand how the internet works, this guide has you covered! ⏱️ Video Chapters: 0:00 - Introduction: What is a Network Port? 1:45 - The 3 Port Ranges (Well-Known, Registered, & Ephemeral) 4:10 - TCP vs. UDP Ports: What’s the difference? 7:30 - Sockets & Transport Layer Multiplexing 10:15 - The "5-Tuple" Explained 13:50 - Network Security: Port Scanning & Firewalls 📖 Key Concepts Covered in This Video: 🔹 What is a Port? In computer networking, a port is a logical endpoint within an operating system that identifies a specific process or network service. Identified by a 16-bit unsigned number, there are 65,536 available ports (ranging from 0 to 65535). They act like entry doors for data—the IP address brings the data to the correct device, and the port directs it to the correct application. 🔹 Port Number Ranges The Internet Assigned Numbers Authority (IANA) categorizes ports into three main ranges: • Well-Known Ports (0–1023): Reserved for essential, standard services like HTTP (Port 80), HTTPS (Port 443), and SSH (Port 22). • Registered Ports (1024–49151): Assigned to user processes or specific applications to prevent network conflicts. • Dynamic / Ephemeral Ports (49152–65535): Temporary ports dynamically assigned by the operating system to client applications (like your web browser) for short-lived outbound connections. 🔹 Sockets & Multiplexing A "Socket" is the combination of an IP Address, a Transport Protocol (like TCP or UDP), and a Port Number. This allows the Transport Layer to perform Multiplexing—the process of assembling data from several different applications and transmitting it over a single network link—and Demultiplexing, which ensures incoming data is routed to the exact right application on the receiving end. 🔹 The 5-Tuple & Session Tracking How does a server handling thousands of connections keep them all straight? It uses the 5-Tuple, a unique fingerprint for every network conversation. The 5-Tuple consists of: 1. Source IP Address 2. Source Port Number 3. Destination IP Address 4. Destination Port Number 5. Protocol (TCP, UDP, ICMP) Firewalls and routers rely heavily on the 5-Tuple to implement access control policies, filter traffic, and manage network performance. 🔹 Port Security & Port Scanning When intruders want to break into a network, they look for open ports—TCP or UDP endpoints configured to accept incoming traffic. Security analysts and bad actors alike use Port Scanners (like Nmap) to probe hosts and identify active services, filtered ports, or vulnerabilities. Properly monitoring your attack surface and limiting open ports behind a firewall is critical to enterprise cybersecurity. 🔗 Resources & Further Reading: • List of TCP and UDP Port Numbers: [IANA Official Registry] • Understanding the OSI Model Transport Layer • Securing Open Ports & Network Baselines 👍 If you found this video helpful, please LIKE and SUBSCRIBE for more IT, Networking, and Cybersecurity tutorials! #ComputerNetworking #TCPUDP #NetworkPorts #CyberSecurity #ITBeginners #CCNA #CompTIA #NetworkEngineering #5Tuple #PortScanning


















![Почему взрываются батарейки и аккумуляторы? [Veritasium]](https://imager.clipsaver.ru/a3-3R9zwyGY/max.jpg)