#51 Hardware Trojans | Information Security 5 Secure Systems Engineering скачать в хорошем качестве
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: #51 Hardware Trojans | Information Security 5 Secure Systems Engineering в качестве 4k
У нас вы можете посмотреть бесплатно #51 Hardware Trojans | Information Security 5 Secure Systems Engineering или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон #51 Hardware Trojans | Information Security 5 Secure Systems Engineering в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
#51 Hardware Trojans | Information Security 5 Secure Systems Engineering
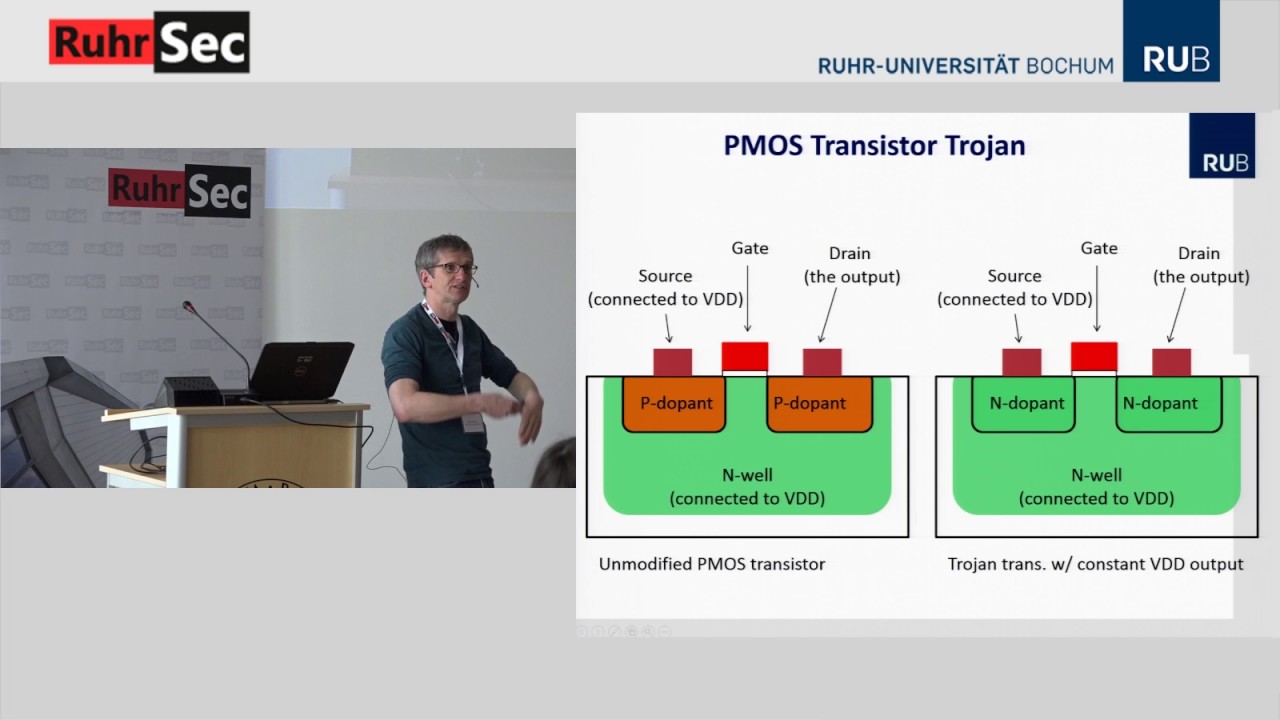
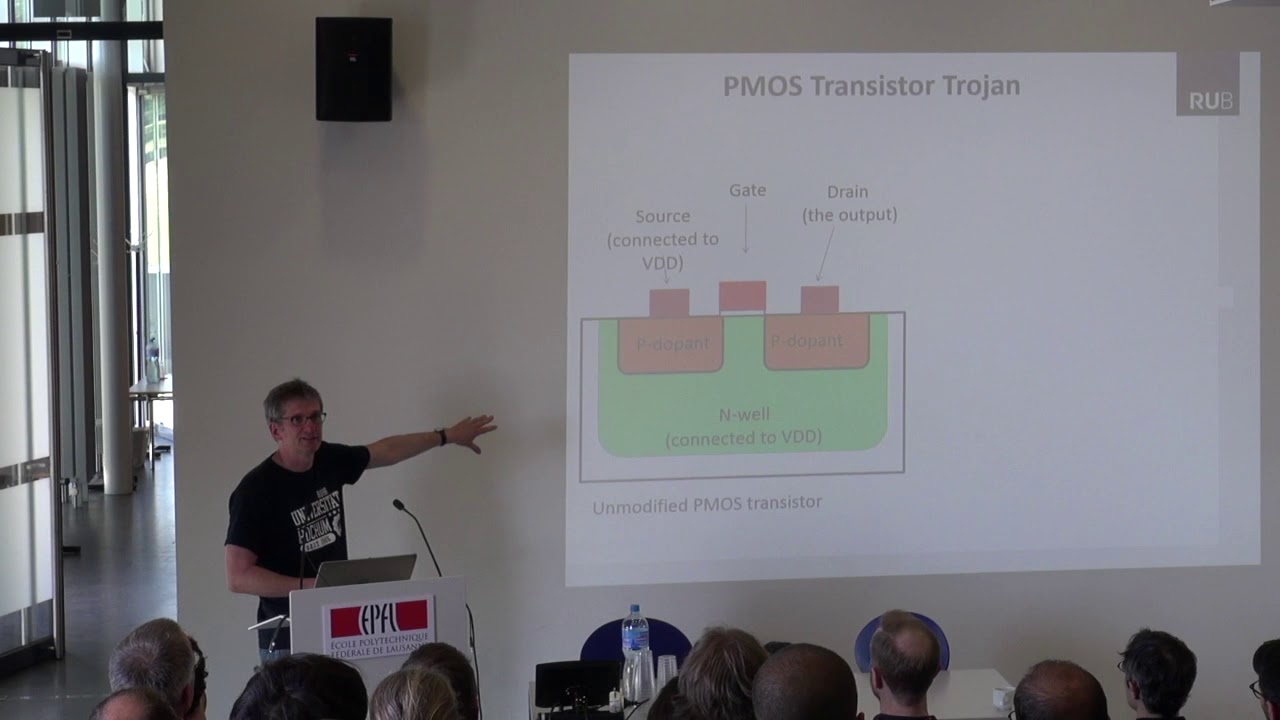
Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture introduces the concept of hardware Trojans, a serious security threat where malicious circuitry is intentionally inserted into hardware designs. It discusses the different stages in the IC design and manufacturing process where hardware Trojans can be introduced, highlighting the challenges associated with detecting and mitigating them. The lecture explains the typical structure of a hardware Trojan, comprising a trigger mechanism and a payload that executes malicious functionality. It then introduces FANCI, a technique for identifying potential hardware Trojan locations within IP cores, emphasizing the importance of automated tools for analyzing complex hardware designs. Viewers will gain an awareness of the threats posed by hardware Trojans and the ongoing research efforts to secure the hardware supply chain. NPTEL Courses permit certifications that can be used for Course Credits in Indian Universities as per the UGC and AICTE notifications. To understand various certification options for this course, please visit https://nptel.ac.in/courses/106106199 #HardwareTrojans #HardwareSecurity #MaliciousHardware #IntegratedCircuits #ICDesign #DetectionTechniques #Trigger #Payload #FANCI