(Podcast) Unmasking the Cisco SD WAN Zero Day CVE 2026 20127 скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: (Podcast) Unmasking the Cisco SD WAN Zero Day CVE 2026 20127 в качестве 4k
У нас вы можете посмотреть бесплатно (Podcast) Unmasking the Cisco SD WAN Zero Day CVE 2026 20127 или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон (Podcast) Unmasking the Cisco SD WAN Zero Day CVE 2026 20127 в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
(Podcast) Unmasking the Cisco SD WAN Zero Day CVE 2026 20127
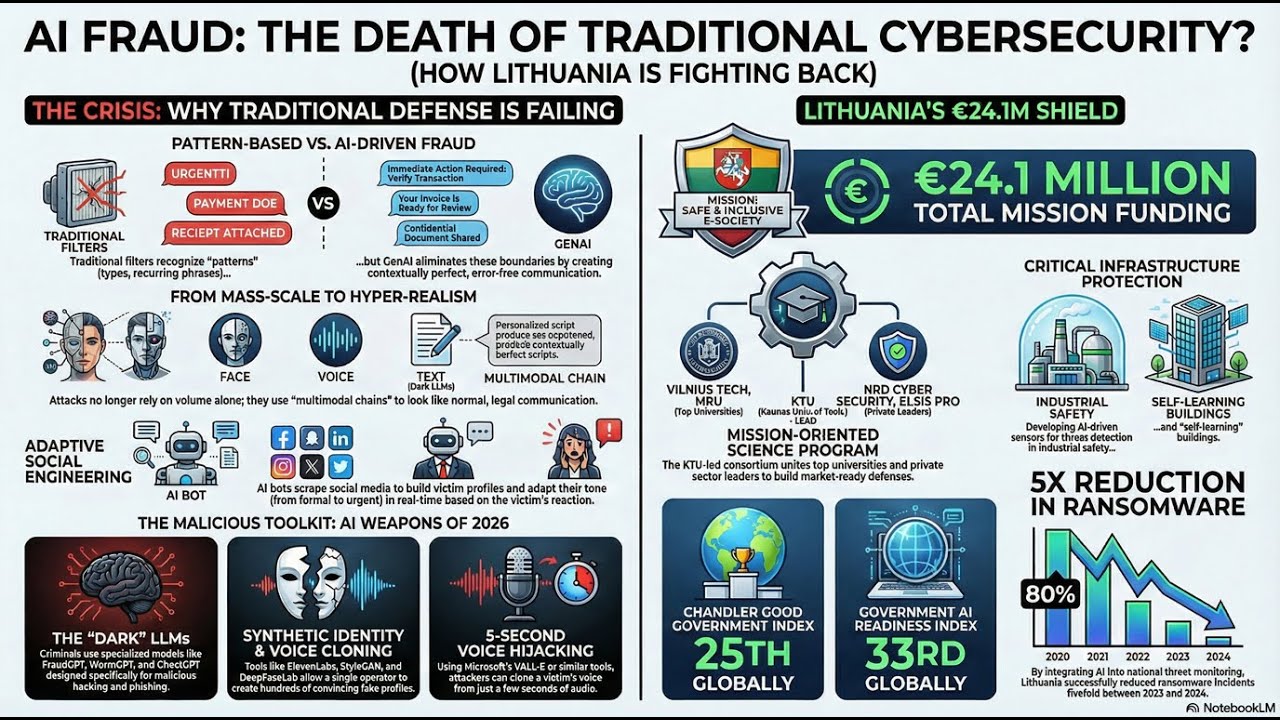
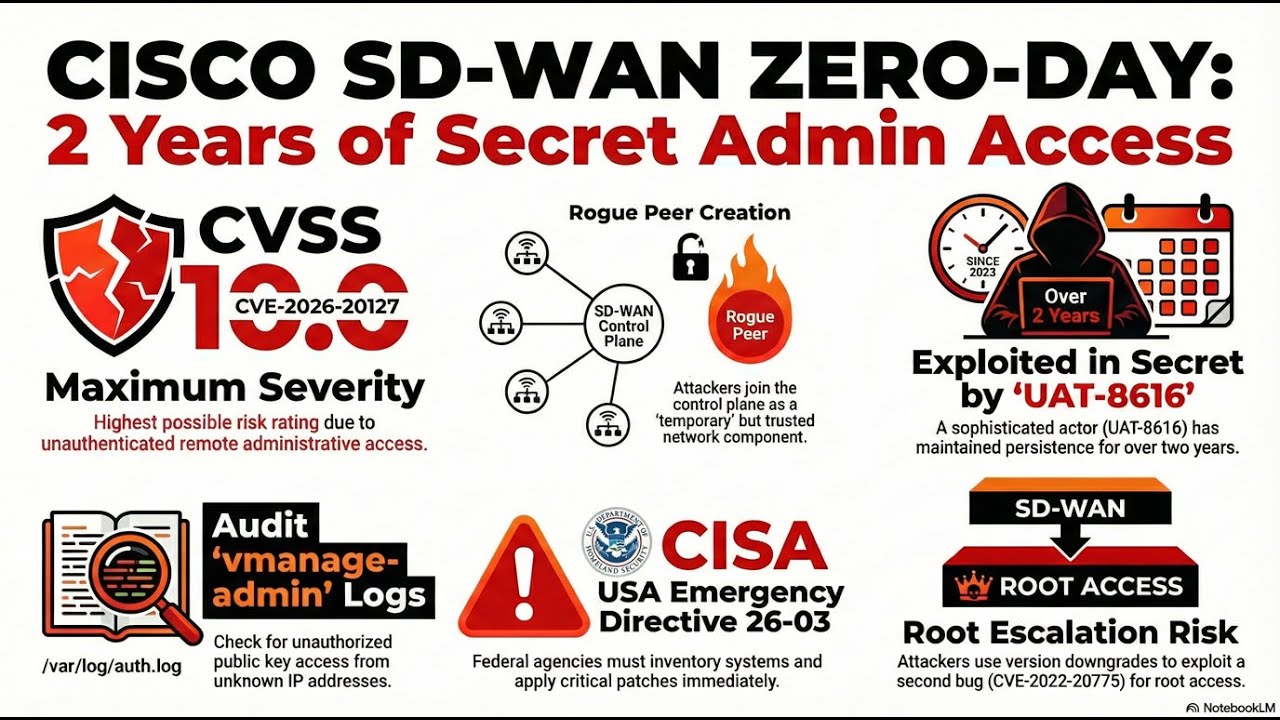
In this episode, we’re breaking down a cybersecurity nightmare that’s been lurking in the shadows since 2023! 🕵️♂️ We are diving deep into CVE-2026-20127—a literal "perfect 10" on the CVSS severity scale hitting Cisco Catalyst SD-WAN (formerly vSmart and vManage)1. Imagine an unauthenticated hacker just waltzing into your network control plane as a "rogue peer" and taking over the entire fabric without an invite. 😱 We explore the sophisticated tactics of the threat actor known as UAT-8616, who didn't just stop at one bug23. These attackers actually downgraded software versions to exploit another vulnerability for root access and then scrubbed the logs to stay invisible! 🧼✨ With CISA issuing Emergency Directive 26-03 and the clock ticking for federal agencies to inventory their systems, this is a high-stakes saga every network admin and security pro needs to hear45. Join us as we unpack how this happened, who is at risk, and the critical steps you need to take to harden your environment! 🛡️🎧 Information sourced from The Hacker News article "Cisco SD-WAN Zero-Day CVE-2026-20127 Exploited Since 2023 for Admin Access" by Ravie Lakshmanan16. #Cisco #CyberSecurity #SDWAN #ZeroDay #CVE202620127 #CISA #Networking #InfoSec #UAT8616 #NetworkSecurity #TechPodcast #VulnerabilityManagement