Why Notes Are Important in Bug Bounty | Bug Bounty Methodology Mapping Using XMind скачать в хорошем качестве
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Why Notes Are Important in Bug Bounty | Bug Bounty Methodology Mapping Using XMind в качестве 4k
У нас вы можете посмотреть бесплатно Why Notes Are Important in Bug Bounty | Bug Bounty Methodology Mapping Using XMind или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Why Notes Are Important in Bug Bounty | Bug Bounty Methodology Mapping Using XMind в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Why Notes Are Important in Bug Bounty | Bug Bounty Methodology Mapping Using XMind
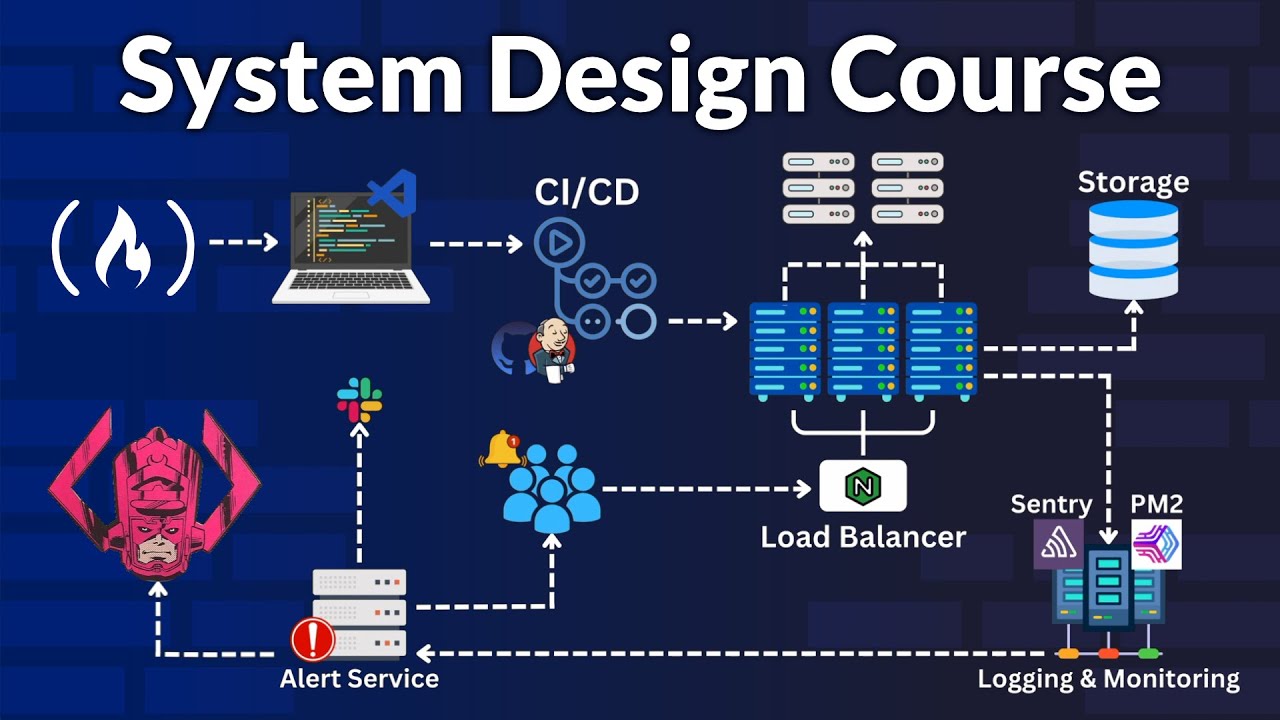
About This Video :- In this video, I explain why taking proper notes is extremely important in Bug Bounty hunting and how notes can help you find more vulnerabilities consistently. I also demonstrate Bug Bounty Methodology Mapping using XMind, showing how to organize recon, attack surface, testing steps, and findings in a clear and structured way. If you are a beginner or intermediate bug bounty hunter, this video will help you: ✅ Build a strong bug bounty workflow ✅ Avoid missing vulnerabilities ✅ Improve recon and testing efficiency ✅ Stay organized using mind maps Tools used: XMind Topic covered: Bug Bounty Notes, Bug Bounty Methodology, Bug Hunting Workflow 📌 This approach is useful for Web Security, Pentesting, and CTF players as well. 🔔 Subscribe for more Bug Bounty & Cybersecurity content. Website : https://cybrige.in Support this channel: https://ko-fi.com/ciphervigil WhatsApp Channel : https://whatsapp.com/channel/0029Vb7N... .......................................................................................................................................................................................................................................................... 🎯 If you want to learn Ethical Hacking for FREE in Hindi, this video will give you a complete overview of our upcoming Ethical Hacking course — designed especially for beginners who want to start their journey in Cybersecurity. 💡 Don’t forget to Subscribe and turn on the notification bell 🔔 to stay updated with all the latest videos and announcements about the course! 📚 Learning Playlists 📌 Ethical Hacking: 👉 Watch Now: • Ethical Hacking 📌 Termux Tutorials: 👉 Watch Now: • Termux Tutorial 📌 Kali Linux Tutorials: 👉 Watch Now: • Termux Tutorial 🔗 Follow Me on Social Media 📸 Instagram: / official_cybrige ⚠️ Note: This video is created only for educational purposes. Please do not misuse the information provided. 💻 Stay Safe on the Internet ⚔️ Stay Legal Always 🔐 Videos on Cyber Security & Technology #bugbountyhunting #bugbountymethodology #bugbountynotes #bugbountyworkflow #xmindbugbounty #bugbountyrecon #howtostartbugbounty #webapplicationsecurity #pentestingmethodology #bughuntingtips #ethicalhackingtutorial #cybersecuritybugbounty bug bounty bug bounty shorts ethical hacking shorts bug bounty methodology bug hunting web security cyber security ethical hacking xmind 📜 Disclaimer This video is for educational purposes only. Copyright Disclaimer Under Section 107 of the Copyright Act 1976: Allowance is made for "fair use" for purposes such as criticism, comment, news reporting, teaching, scholarship, and research. Fair use is permitted by copyright statute that might otherwise be infringing. Non-profit, educational, or personal use tips the balance in favor of fair use. Thank you, Cybrige 👍 LIKE | SUBSCRIBE | SHARE | COMMENT #BugBounty #BugBountyMethodology #EthicalHacking #BugBountyNotes #BugBountyWorkflow #XMind #BugHunting #WebSecurity #Pentesting #CyberSecurity #BugBountyIndia #EthicalHackingIndia #CyberSecurityIndia #HackingTutorial #BugBountyTips #BugBounty #BugBountyMethodology #EthicalHacking #BugBountyNotes #BugBountyWorkflow #XMind #BugHunting #WebSecurity #Pentesting #CyberSecurity #BugBountyIndia #EthicalHackingIndia