Day 44 of Becoming a SOC Analyst | They Replaced Utilman.exe With CMD — SYSTEM Shell Before Login скачать в хорошем качестве
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Day 44 of Becoming a SOC Analyst | They Replaced Utilman.exe With CMD — SYSTEM Shell Before Login в качестве 4k
У нас вы можете посмотреть бесплатно Day 44 of Becoming a SOC Analyst | They Replaced Utilman.exe With CMD — SYSTEM Shell Before Login или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Day 44 of Becoming a SOC Analyst | They Replaced Utilman.exe With CMD — SYSTEM Shell Before Login в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Day 44 of Becoming a SOC Analyst | They Replaced Utilman.exe With CMD — SYSTEM Shell Before Login
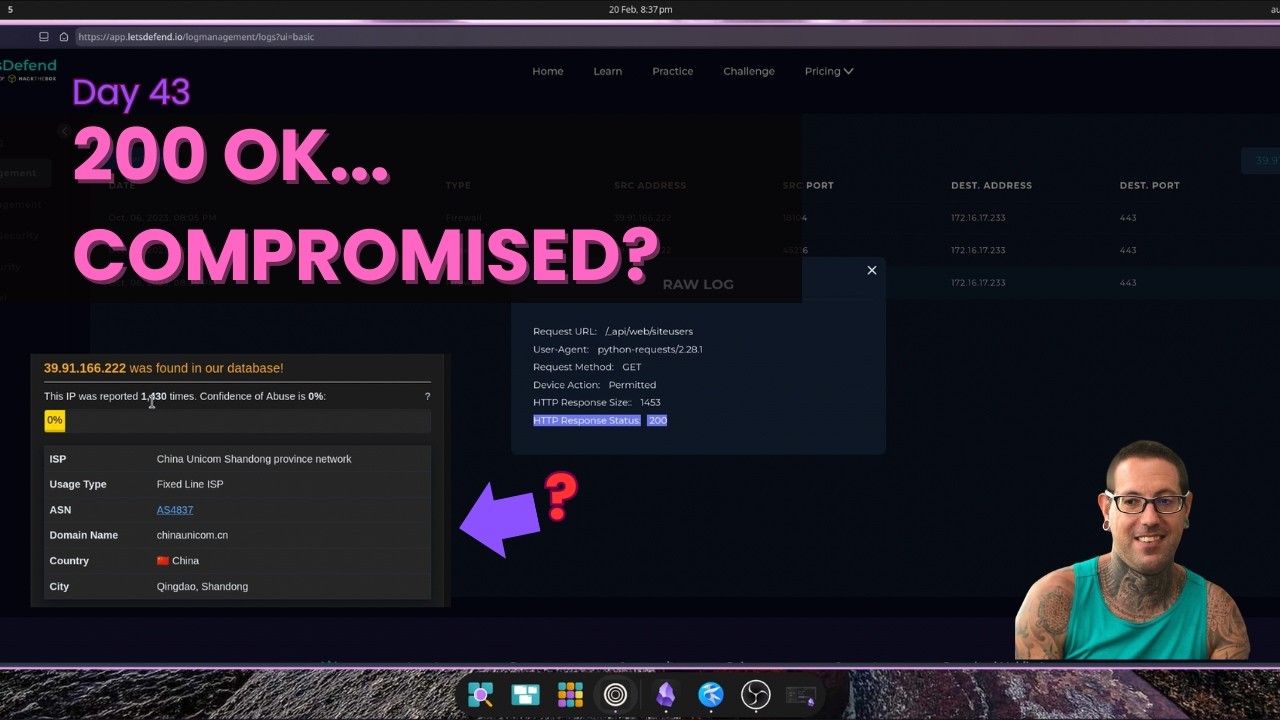
Day 44 of Becoming a SOC Analyst — Utilman.exe Winlogon LOLBin Exploit (True Positive) Classic LOLBin abuse — an attacker replaced the Windows accessibility binary Utilman.exe with cmd.exe, rebooted the host, and obtained a SYSTEM-level shell from the login screen before any authentication. From there they created a new local admin account (superman / onepunch123) and added it to the administrators group. The whole thing flew under the radar because it used a legitimate Windows binary. Walked through LOLBin identification, parent process analysis (Winlogon.exe spawning Utilman.exe is never normal), MITRE mapping (T1546.008, T1136, T1068), and full containment — account removal, binary restoration, host isolation. --- Scenario sourced from LetsDefend.io — one of the best hands-on SOC analyst training platforms out there. Highly recommend if you're on the same path. I'm documenting every day of my journey to landing a Level 1 SOC Analyst role — the wins, the grinds, and everything in between. 🔵 What I Cover Threat Detection · Alert Triage · SIEM Analysis · PCAP Review · Incident Response · Blue Team Tools 🚨 Open to Work — Seeking a Level 1 SOC Analyst role in Melbourne or Remote (AU) 📂 Portfolio → inksec.io 💼 LinkedIn → linkedin.com/in/tate-pannam-8b64b23a3 If you chose the red pill... 0x74617465.sh #SOCAnalyst #BlueTeam #Cybersecurity #LOLBins #PrivilegeEscalation #WindowsSecurity #IncidentResponse #SIEM #Day44 #CyberSecurityJourney #Melbourne #LetsDefend #LetsDefendSOC #Utilman #AccessibilityFeatures