ADCS NTLM Relay - Compromise the DC скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: ADCS NTLM Relay - Compromise the DC в качестве 4k
У нас вы можете посмотреть бесплатно ADCS NTLM Relay - Compromise the DC или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон ADCS NTLM Relay - Compromise the DC в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
ADCS NTLM Relay - Compromise the DC
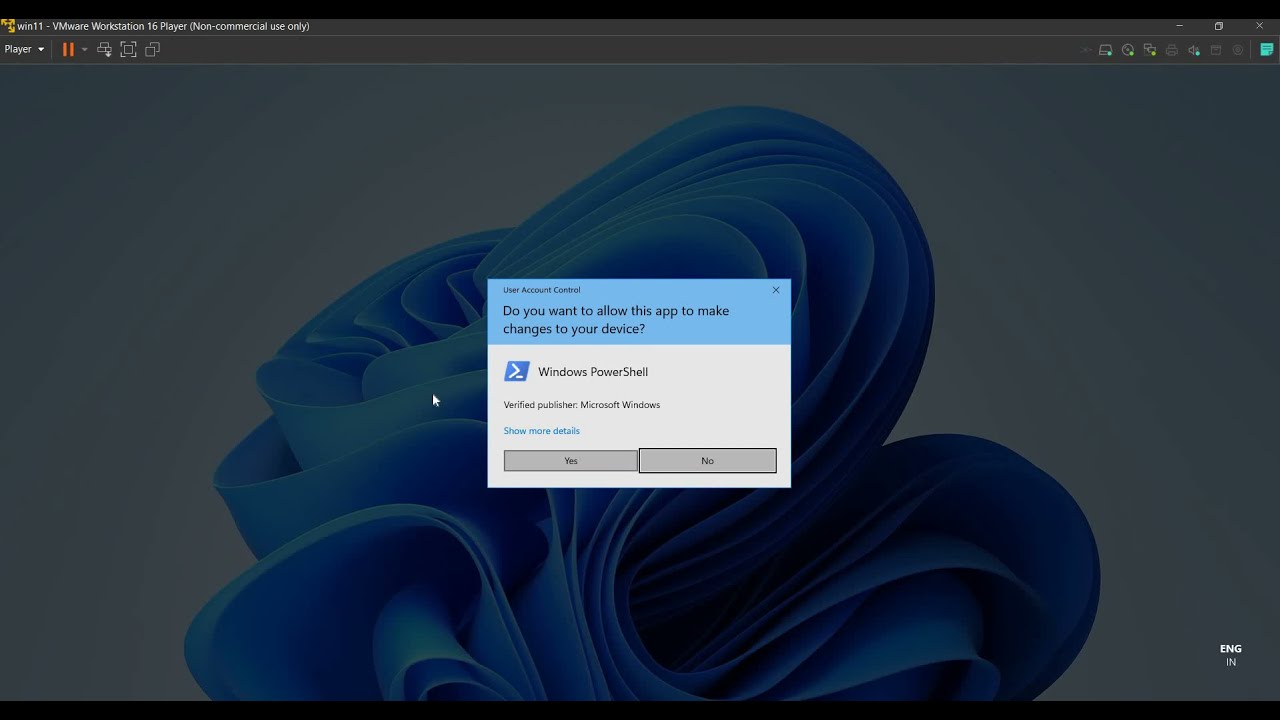
NTLM relay based attacks had always been a problem to solve by Microsoft, and just few days another NTLM relay attack is being discovered which used ADCS HTTP Endpoints, which will help an attacker to request the certificate and then can use that base-64 certificate to embed the authenticated ticket to the current user session which will authenticate the user to the DC. and then the attacker can request the NTLM hashes of the users like krbtgt account or Administrator etc. To demonstrate this attack, you can use any method which you guys are comfortable with like Petitpotam, print spooler, HTTP req, etc. I will be demonstrating with "Print Spooler", as recently I was able to bypass defender to replicate this attack. For easiness, you can use below script: https://github.com/NotMedic/NetNTLMto... Now there are few constraints that we have to take care to replicate the attack in a real-time domain: 1. The victim should be a part of domain. 2. The certificate template request should be allowed for the "domain\users" or "domain\victim". Now there is a very beautiful blog explanation given to explore more on this. Have a look. https://dirkjanm.io/ntlm-relaying-to-... PS - The demonstration is for educational or Red-Team purposes.