Running a Bug Bounty Program: What Works, What Fails, and What No One Tells You скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Running a Bug Bounty Program: What Works, What Fails, and What No One Tells You в качестве 4k
У нас вы можете посмотреть бесплатно Running a Bug Bounty Program: What Works, What Fails, and What No One Tells You или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Running a Bug Bounty Program: What Works, What Fails, and What No One Tells You в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Running a Bug Bounty Program: What Works, What Fails, and What No One Tells You
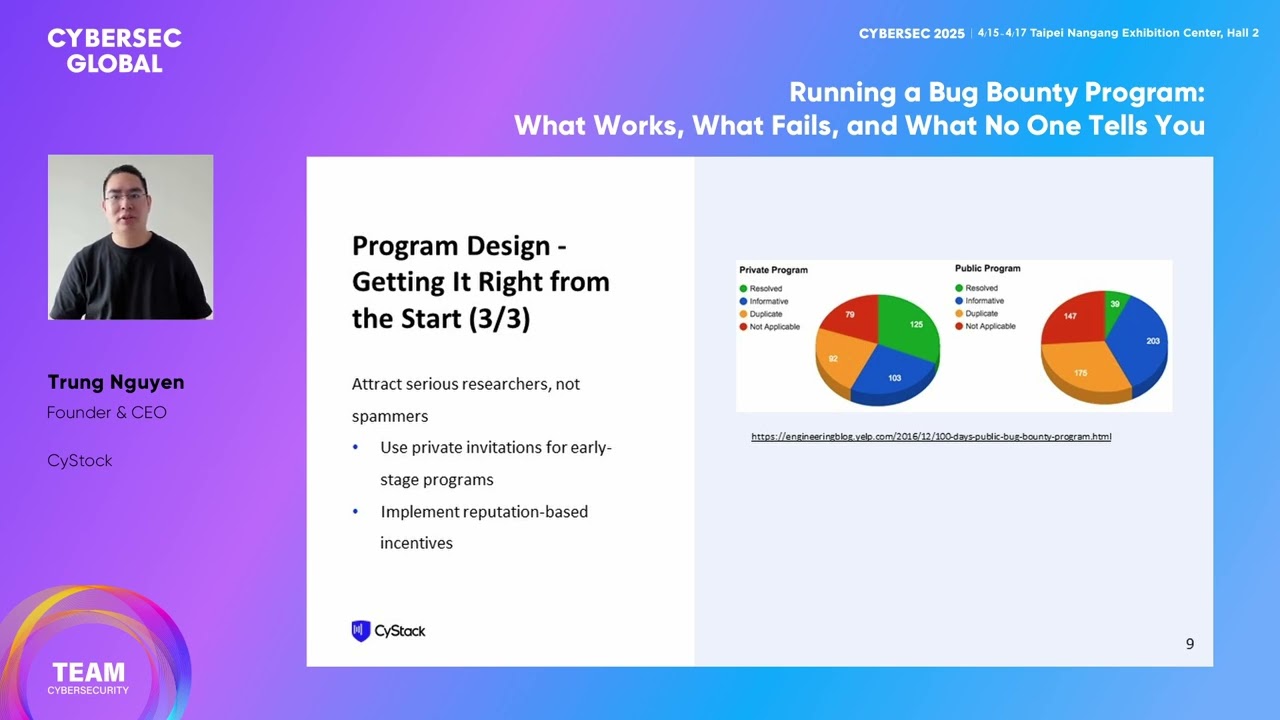
Trung Nguyen / Founder & CEO, CyStack Bug bounty programs are a double-edged sword. Done right, they uncover critical vulnerabilities before attackers do. Done wrong, they create noise, drain resources, and even introduce new security risks. So how do you build a bug bounty program that actually works? Drawing from my experience running Vietnam’s first and largest bug bounty platform, this session will cut through the theory and dive into the real-world lessons of designing, securing, and scaling a successful program. We’ll cover: 1. Program Design: How to define scope, set fair rewards, and attract serious security researchers - not just low-effort spam. 2. Vulnerability Handling: Triage strategies to separate signal from noise, manage false positives, and deal with duplicate reports effectively. 3. Operational Security Risks: How to prevent abuse, secure your own bug bounty infrastructure, and avoid becoming a target yourself. 4. The Human Factor: What motivates researchers, how to build trust, and why community management is just as important as technical execution. We'll also discuss hard lessons learned, like how to handle rogue submissions and why transparency can make or break your program. By the end of this talk, you’ll walk away with a practical, tested framework for building a bug bounty program that is secure, efficient, and actually useful - whether you’re starting from scratch or improving an existing initiative. #Bug Bounty #Hackers & Threats #Vulnerability Management https://cybersec.ithome.com.tw/en