Essential Penetration Testing Tools for Web Application Security скачать в хорошем качестве
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Essential Penetration Testing Tools for Web Application Security в качестве 4k
У нас вы можете посмотреть бесплатно Essential Penetration Testing Tools for Web Application Security или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Essential Penetration Testing Tools for Web Application Security в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Essential Penetration Testing Tools for Web Application Security
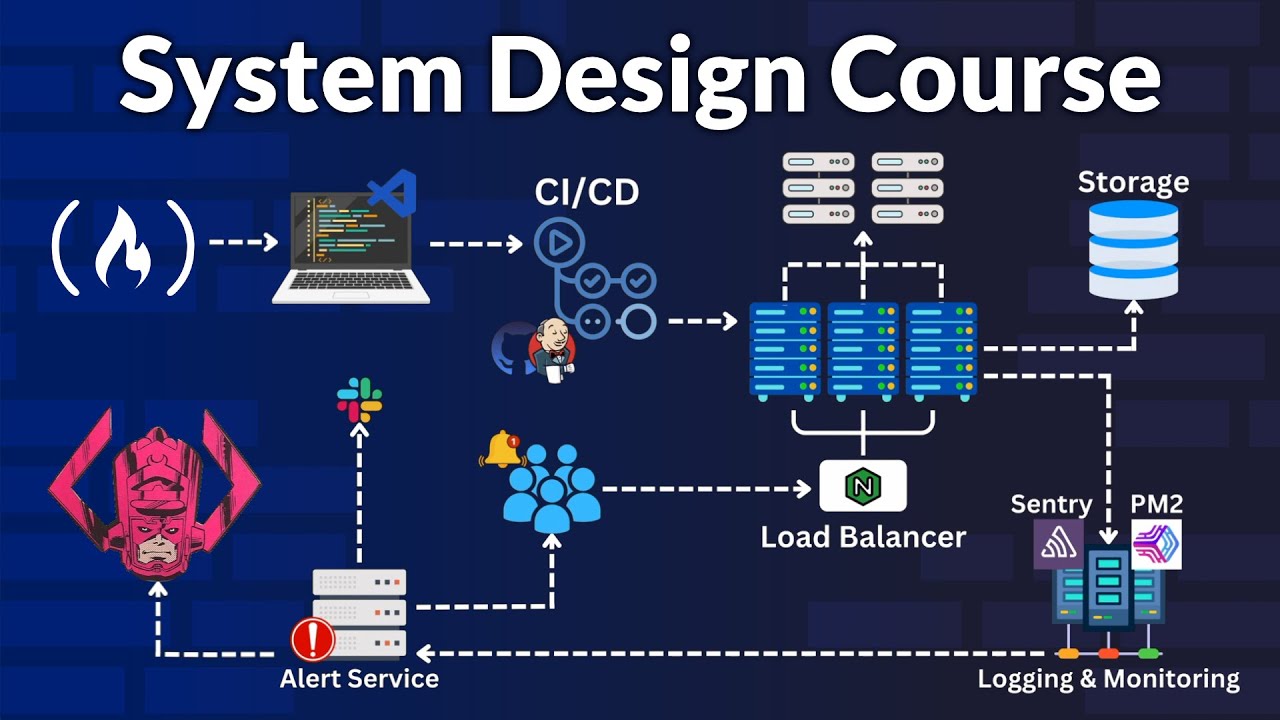
Summary: Discover an essential list of penetration testing tools, including open source options, that are crucial for ensuring the security of your web applications. --- Essential Penetration Testing Tools for Web Application Security In today's digital landscape, the security of web applications is paramount. Penetration testing, often referred to as ethical hacking, involves evaluating the security of a system by simulating an attack from malicious outsiders. Penetration testing tools play a crucial role in this process, helping security professionals identify and mitigate potential vulnerabilities. Here, we provide an essential list of both commercial and open-source penetration testing tools that are invaluable for web application security. Burp Suite Burp Suite is a comprehensive tool for web application security testing. It includes a variety of utilities that support every phase of the testing process, from initial mapping to finding and exploiting security vulnerabilities. While Burp Suite comes in both free and paid versions, the free edition is quite powerful and widely used. OWASP ZAP OWASP ZAP (Zed Attack Proxy) is an open-source penetration testing tool for web applications. Developed under the Open Web Application Security Project, it is designed to find and fix security vulnerabilities automatically. ZAP is a popular choice among security professionals and developers due to its ease of use, extensive documentation, and powerful features. Metasploit Framework Metasploit Framework is an open-source tool used for developing and executing exploit code against a remote target machine. It is highly popular among penetration testers due to its vast collection of exploits and payload options. Metasploit assists in discovering and validating vulnerabilities, making it an invaluable resource in a penetration tester's toolkit. Nmap Nmap (Network Mapper) is an open-source utility that has long been a staple of the security community. It is used for network discovery and security auditing, capable of identifying hosts and services on a network. For web application penetration testing, Nmap enables testers to discover and enumerate hosts and services, identify open ports, and map out the network topology. SQLmap SQLmap is an open-source penetration testing tool designed specifically for identifying and exploiting SQL injection vulnerabilities in web applications. It automates the process of detecting and exploiting SQL injection flaws, enabling penetration testers to take over database servers efficiently. Hydra Hydra is a powerful and flexible login cracker that supports numerous protocols and services. It helps penetration testers perform brute-force password attacks against various services such as HTTP, HTTPS, FTP, and SSH. While brute-force attacks are noisy and generally easy to detect, Hydra is a valuable tool for auditing the strength of password policies and user credentials. John the Ripper John the Ripper is an open-source password cracker frequently used for password recovery and security auditing. It is notable for its ability to crack weak passwords and support a wide range of password hash types. For web application penetration testing, it can be used to audit the security of stored user credentials. Conclusion Equipped with the right penetration testing tools, security professionals can ensure the robustness of web applications against potential attacks. While our list includes just a few of the many available penetration testing tools, these options are a solid starting point for anyone looking to enhance their web application security posture. By incorporating these tools into regular security assessments, organizations can proactively identify and mitigate vulnerabilities, safeguarding their web applications from potential threats.







![Best of Deep House [2026] | Melodic House & Progressive Flow](https://imager.clipsaver.ru/Il-ZpBuC8tA/max.jpg)