Off-By-One 2024 Day 1- Ghost in the BLF:A 2 year journey of chasing in the wild LPE exploits скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Off-By-One 2024 Day 1- Ghost in the BLF:A 2 year journey of chasing in the wild LPE exploits в качестве 4k
У нас вы можете посмотреть бесплатно Off-By-One 2024 Day 1- Ghost in the BLF:A 2 year journey of chasing in the wild LPE exploits или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Off-By-One 2024 Day 1- Ghost in the BLF:A 2 year journey of chasing in the wild LPE exploits в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Off-By-One 2024 Day 1- Ghost in the BLF:A 2 year journey of chasing in the wild LPE exploits
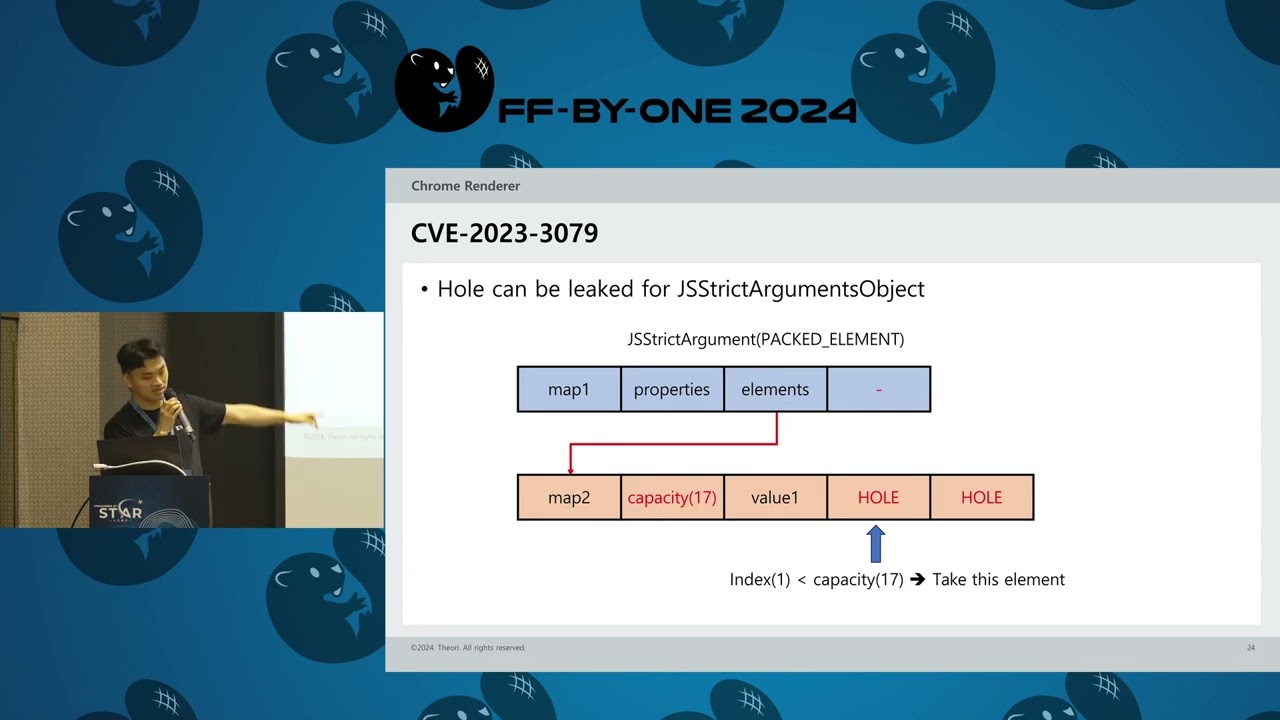
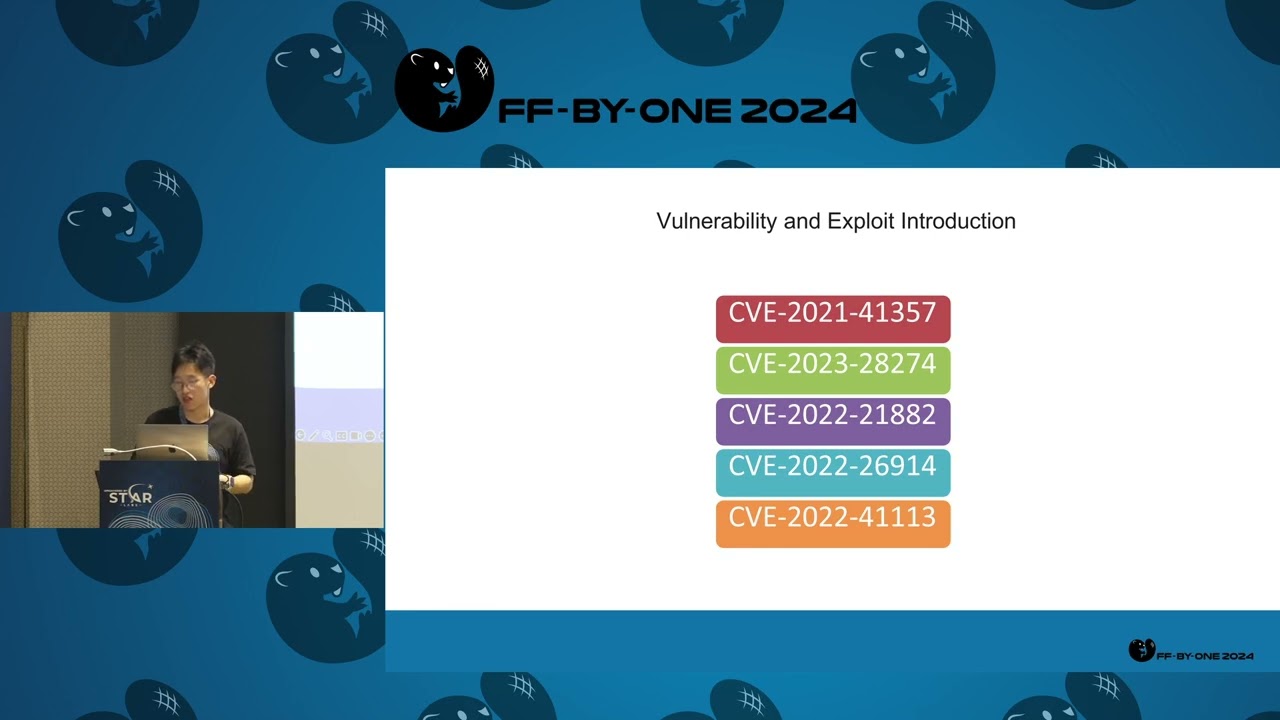
Ghost in the BLF: A two-year journey of chasing in-the-wild LPE exploits in Windows CLFS Abstract Since October 2021, we have been continuously chasing the latest in-the-wild Windows CLFS (Common Log File System) LPE exploits. During this process, we captured two in-the-wild Windows CLFS 0days and at least seven in-the-wild Windows CLFS 1days. Meanwhile, through variant analysis of the itw exploits, we identified two new CLFS vulnerabilities and reported them to Microsoft. Interestingly, two of the captured 1day exploits utilized the vulnerabilities that we discovered through variant analysis. In this talk, we will share how we are using the combination of “threat hunting” and “variant analysis” to assist Microsoft in patching four CLFS 0day vulnerabilities (two in-the-wild 0days and two independently discovered 0days). We believe that the approach combining “threat hunting” and “variant analysis” is more effective than traditional defense methods, and we want to share our practical and insights into this process: why we selected CLFS vulnerabilities, how we chased in-the-wild CLFS exploits, how we analyzed captured vulnerability exploits, and how we conduct variant analysis. At the end of this talk, we will incorporate the latest findings to give some insights on the in-the-wild Windows LPE 0days trends. Speakers Quan Jin is a security research expert from DBAPPSecurity WeBin Lab. His interests are vulnerability research and itw 0day hunting. He has received more than 40 CVE acknowledgments from Microsoft/Adobe/Apple, and has been listed as a MSRC Most Valuable Security Researcher for three years(2020-2022). He once spoke at Bluehat Shanghai 2019, HITB2021AMS/HITB2023AMS and BlackHat USA 2022/BlackHat Asia 2024. Yingqi Shi is an undergraduate senior majoring in Computer Science, currently serving as a security research intern at DBAPPSecurity. His main research areas include binary analysis, vulnerability discovery & exploitation and reverse engineering. He excels particularly in reverse engineering. He is a core member of the Nu1L Team, achieving excellent results in numerous top-tier CTF (Capture The Flag) events both domestically and internationally. He once spoke at BlackHat Asia 2024 Guoxian Zhong is a senior security engineer at DBAPPSecurity WeBin Lab. His main research areas include binary analysis, reverse engineering and vulnerability discovery & exploitation. He once spoke at BlackHat Asia 2024.