SOAR with Jamf Protect: Automated Security Response Workflows for macOS скачать в хорошем качестве
Повторяем попытку...
Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: SOAR with Jamf Protect: Automated Security Response Workflows for macOS в качестве 4k
У нас вы можете посмотреть бесплатно SOAR with Jamf Protect: Automated Security Response Workflows for macOS или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон SOAR with Jamf Protect: Automated Security Response Workflows for macOS в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
SOAR with Jamf Protect: Automated Security Response Workflows for macOS
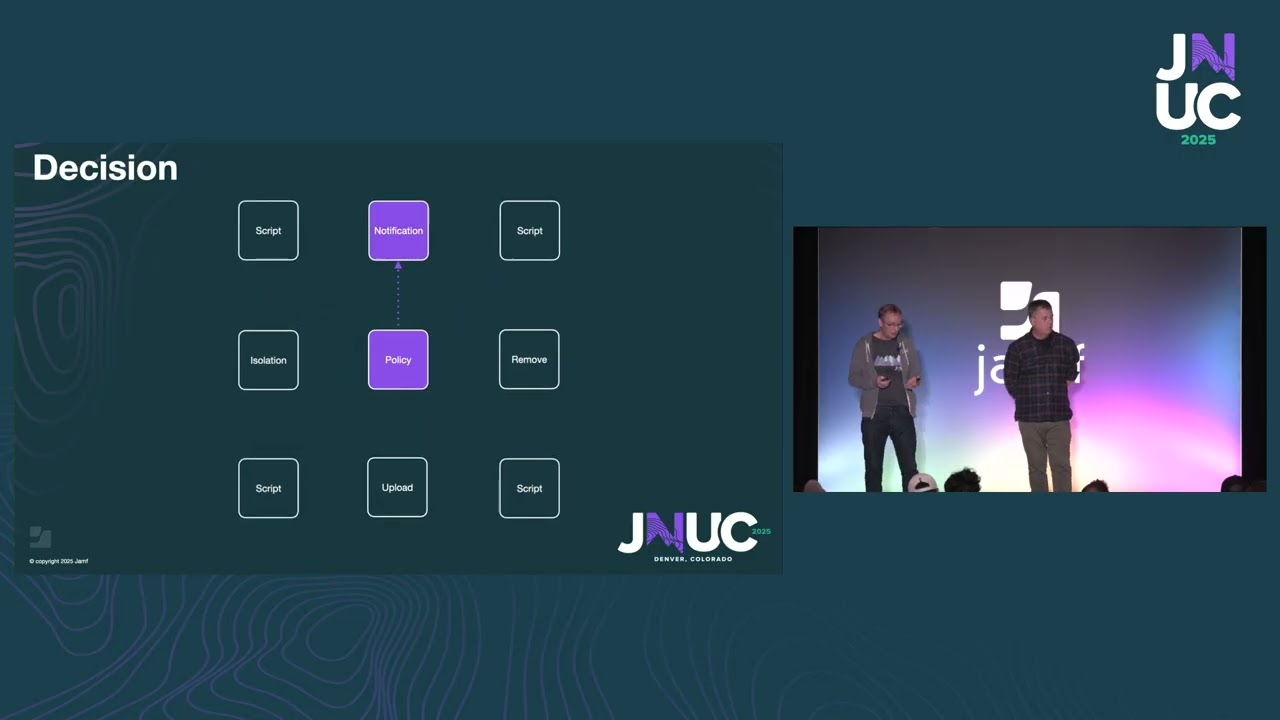
Build Security Orchestration, Automation, and Response (SOAR) workflows for #macOS endpoints using Jamf Protect and Jamf Pro. Peter Argyle (Learning Experience Designer) and Richard Mallion (Senior Education Services Engineer) from Jamf demonstrate three real-world playbooks for automated incident response: network isolation, quarantined file acquisition, and forensic data collection with Aftermath. Learn how to detect malicious behavior, trigger automated remediation policies, and collect forensic evidence without manual intervention. What you'll learn: ► Understanding SOAR (Security, Orchestration, Automation, Response) functionality ► Configuring Jamf Protect analytics to detect security threats ► Building automated remediation workflows between Jamf Protect and Jamf Pro ► Creating smart groups with extension attributes for threat detection ► Implementing network isolation for compromised Mac endpoints ► Handling quarantined malware with automated upload to S3 buckets ► Collecting forensic data using Aftermath framework ► Notifying users during security incidents with IBM Notifier ► Managing packet filter (PF) firewall rules for endpoint isolation 0:00 Introduction: Soaring with Jamf Protect 0:42 What is SOAR? Security, Orchestration, Automation, Response 2:32 Jamf Protect Security Portals: macOS Security and Jamf Security Cloud 3:34 Jamf Pro: Apple Device Management at Scale 4:26 Workflow Step-by-Step: Screenshot Detection Example 8:06 Configuring Remediation Policies with Custom Triggers 9:15 Workflow Recap: From Detection to Remediation 10:06 Remediation Options: Notifications, File Removal, Isolation, Scripts 11:04 Playbook 1: Network Isolation for Compromised Endpoints 20:41 Playbook 2: Quarantined File Acquisition and Removal 24:25 Playbook 3: Forensic Data Collection with Aftermath 28:43 Admin Workflow: Analyzing Uploaded Forensic Reports 29:02 Jamf Training Courses: Security Products (170, 270, 370) 30:06 Q&A Session #cybersecurity #endpointsecurity #incidentresponse #macossecurity #endpointprotection #jamf