Scoping an Intrusion Using Identity Host and Network Indicators SANS скачать в хорошем качестве
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Scoping an Intrusion Using Identity Host and Network Indicators SANS в качестве 4k
У нас вы можете посмотреть бесплатно Scoping an Intrusion Using Identity Host and Network Indicators SANS или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Scoping an Intrusion Using Identity Host and Network Indicators SANS в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Scoping an Intrusion Using Identity Host and Network Indicators SANS
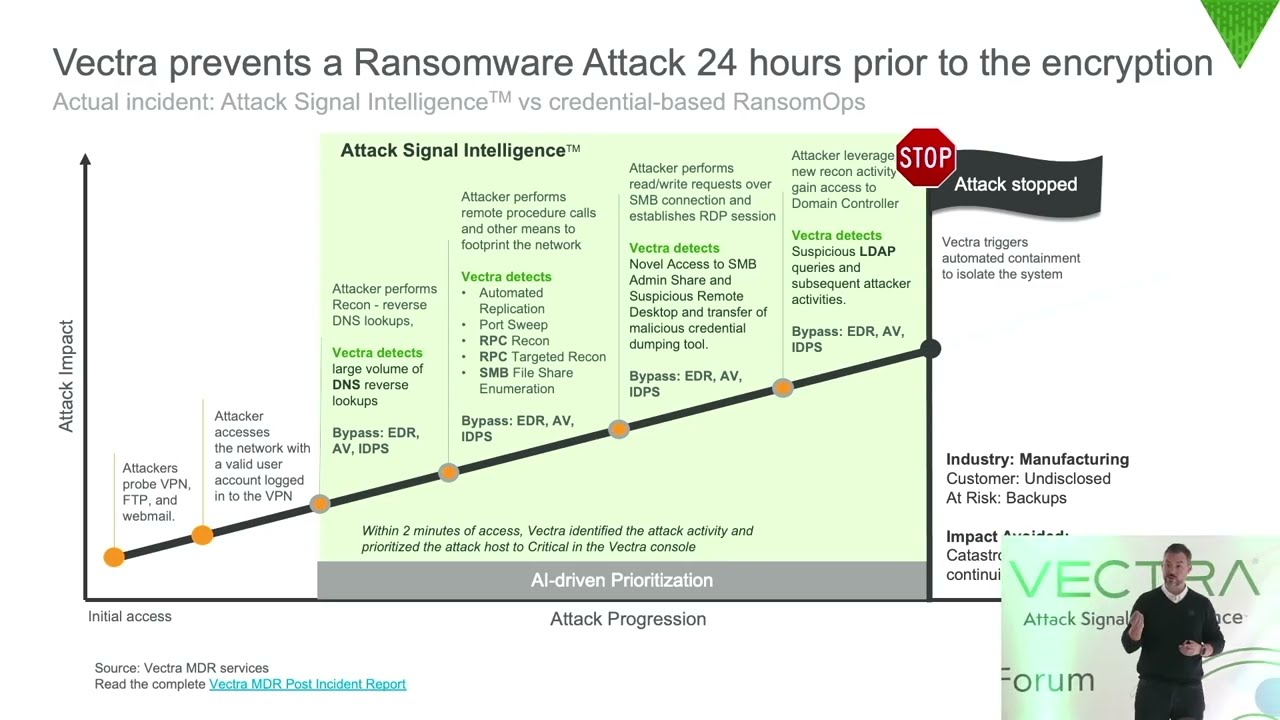
An extension of SANS’ “Hunting in Network Telemetry” on how to hunt for compromised assets within network telemetry, this webcast covers post identification activities to effectively determine the scope of an intrusion. In this video with SANS Instructor Chris Crowley, and principal security engineer at Vectra AI, Dale O’Grady, you will learn: ► Techniques for scoping an incident once discovered ► Sources available on the network and endpoints for identification of adversary infrastructure ► How Vectra can help differentiate misuse of privilege from normal use of privilege to determine threats from adversaries More information: www.vectra.ai ► Website: https://www.vectra.ai/products/platform ► Security-led AI finds attackers across your business: https://www.vectra.ai/products/how-we... ► Blog: https://www.vectra.ai/blogpost/time-t... ► Vectra metadata attributes and their descriptions: https://content.vectra.ai/hubfs/downl... About Vectra AI Vectra® is a cybersecurity leader in threat detection and response for hybrid and multi-cloud enterprises. The Vectra platform uses AI to detect threats at speed across public cloud, identity, SaaS applications, and data centers. Only Vectra optimizes AI to detect attacker methods—the TTPs at the heart of all attacks—rather than simplistically alerting on “different”. The resulting high-fidelity threat signal and clear context enables security teams to respond to threats sooner and to stop attacks in progress faster. Organizations worldwide rely on Vectra for cybersecurity resilience in the face of dangerous cyber threats and to prevent ransomware, supply chain compromise, identity takeovers, and other cyberattacks from impacting their businesses. For more information, visit vectra.ai.