Setting Up Egress for Your Kubernetes Cluster скачать в хорошем качестве
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Setting Up Egress for Your Kubernetes Cluster в качестве 4k
У нас вы можете посмотреть бесплатно Setting Up Egress for Your Kubernetes Cluster или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Setting Up Egress for Your Kubernetes Cluster в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
Setting Up Egress for Your Kubernetes Cluster
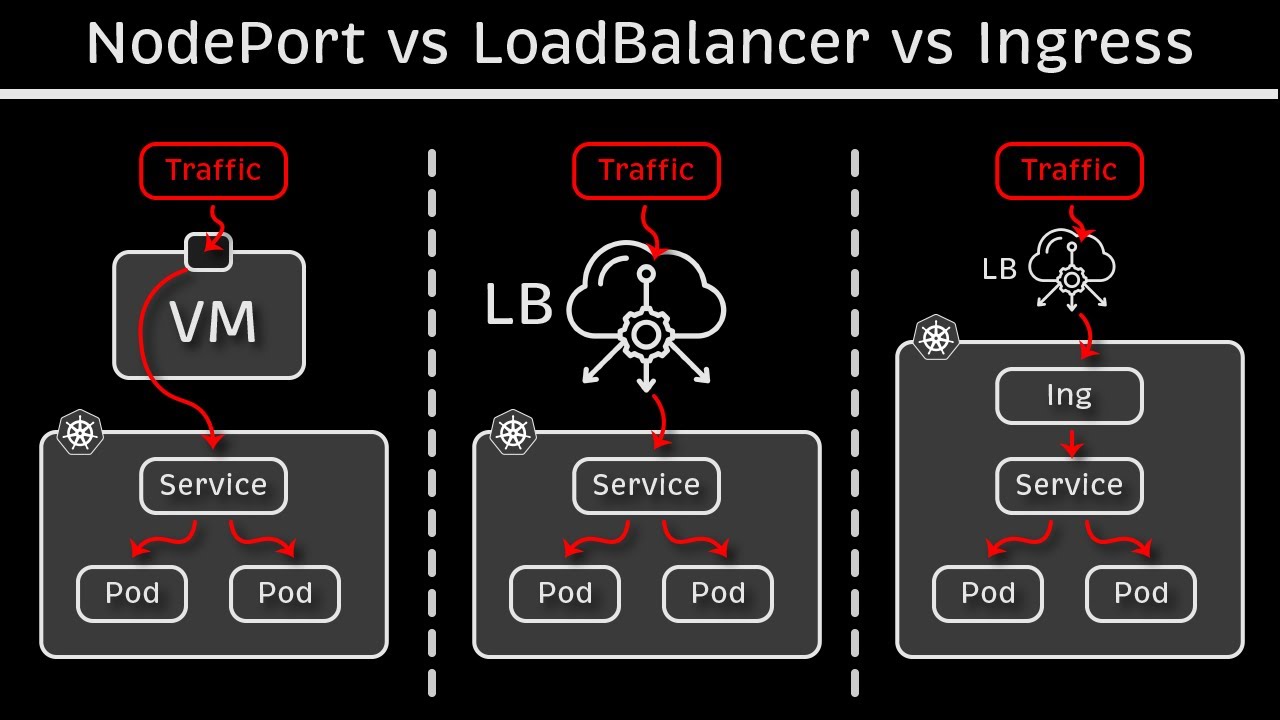
Learn how to configure egress for your Kubernetes cluster to enable external communication for your applications securely and efficiently. --- This video is based on the question https://stackoverflow.com/q/73893197/ asked by the user 'CraZyCoDer' ( https://stackoverflow.com/u/16591513/ ) and on the answer https://stackoverflow.com/a/73905081/ provided by the user 'Mike' ( https://stackoverflow.com/u/20068808/ ) at 'Stack Overflow' website. Thanks to these great users and Stackexchange community for their contributions. Visit these links for original content and any more details, such as alternate solutions, latest updates/developments on topic, comments, revision history etc. For example, the original title of the Question was: What I need to provide to make calls from my k8s cluster? Also, Content (except music) licensed under CC BY-SA https://meta.stackexchange.com/help/l... The original Question post is licensed under the 'CC BY-SA 4.0' ( https://creativecommons.org/licenses/... ) license, and the original Answer post is licensed under the 'CC BY-SA 4.0' ( https://creativecommons.org/licenses/... ) license. If anything seems off to you, please feel free to write me at vlogize [AT] gmail [DOT] com. --- Understanding Egress in Kubernetes As Kubernetes (k8s) becomes a fundamental part of infrastructure in many organizations, you may encounter questions about networking in specific environments. For example, you might wonder how your application running inside a Kubernetes cluster can access external resources, particularly when everything is contained within a VPN. That's where the concept of egress comes in. In this guide, we’ll explore how to properly set up egress from your Kubernetes cluster to allow your applications to communicate with a host machine outside the cluster. We will clarify what you need to configure and provide you with steps to ensure a seamless setup. The Challenge of Egress When deploying applications in Kubernetes, it's crucial to understand the connectivity between your applications and external resources. In this case, the user has a Kubernetes cluster with An application running inside it. A need to access a host machine within the same VPN network. The question arises: How do you allow your application to send requests to the host machine? This question revolves around configuring egress correctly to enable outbound traffic while potentially maintaining security through network policies. What You Need to Know About Egress Default Behavior of Kubernetes Networking Out of the box, Kubernetes allows all network connectivity between pods, services, and external computers unless you specifically configure it otherwise. Here are some key points: Default Access: By default, Kubernetes permits both ingress (incoming traffic) and egress (outgoing traffic) unless you have implemented Network Policies to restrict access. Access to Applications: If you have deployed your application but have not exposed it via services like Ingress or LoadBalancer type services, external systems won’t be able to access it directly. Egress Configuration Steps To successfully set up egress for your application, follow these organized steps: Verify Network Policies: If you have not enabled any Network Policies, your application should communicate without any barriers. If there are policies enforced, review them to ensure they allow egress communication. Expose the Application: To make your application reachable from outside the cluster, you must expose it properly. Use one of the following methods: Service of Type LoadBalancer: If you are running on a cloud provider, create a service of type LoadBalancer to expose your application externally. Ingress Controller: For on-premise setups or more complex routing needs, install an Ingress Controller that facilitates HTTP and HTTPS routing to services within the Kubernetes cluster. Using MetalLB: If you're running your Kubernetes cluster on-premises and want to expose your service as a LoadBalancer, you can use MetalLB. It provides a way to allocate external IPs, making it easier to expose services. Conclusion Configuring egress for your Kubernetes applications is essential for connecting to external services and resources. By understanding the default behavior of Kubernetes networking and following the outlined steps, you can set up egress to enable your applications to communicate effectively with your host machine or any other external service. Final Thoughts It's important to consider security when allowing egress traffic. Regularly review your Network Policies, and ensure that only the necessary connections are permitted. This adds a layer of security while enabling essential functionalities. By following this guide, you should be on your way to successfully facilitating egress for your Kubernetes applications. If you have further questions, feel free to ask in the community!





![[4K FULL HD] Relaxing Water Background | 1 HOUR | Calm Water Wallpaper (No Sound)](https://imager.clipsaver.ru/y9PTNTSpGJs/max.jpg)