Learn How Hackers Delete Activity Logs and Remove Traces of Their Actions скачать в хорошем качестве
Повторяем попытку...

Скачать видео с ютуб по ссылке или смотреть без блокировок на сайте: Learn How Hackers Delete Activity Logs and Remove Traces of Their Actions в качестве 4k
У нас вы можете посмотреть бесплатно Learn How Hackers Delete Activity Logs and Remove Traces of Their Actions или скачать в максимальном доступном качестве, видео которое было загружено на ютуб. Для загрузки выберите вариант из формы ниже:
-
Информация по загрузке:
Скачать mp3 с ютуба отдельным файлом. Бесплатный рингтон Learn How Hackers Delete Activity Logs and Remove Traces of Their Actions в формате MP3:
Если кнопки скачивания не
загрузились
НАЖМИТЕ ЗДЕСЬ или обновите страницу
Если возникают проблемы со скачиванием видео, пожалуйста напишите в поддержку по адресу внизу
страницы.
Спасибо за использование сервиса ClipSaver.ru
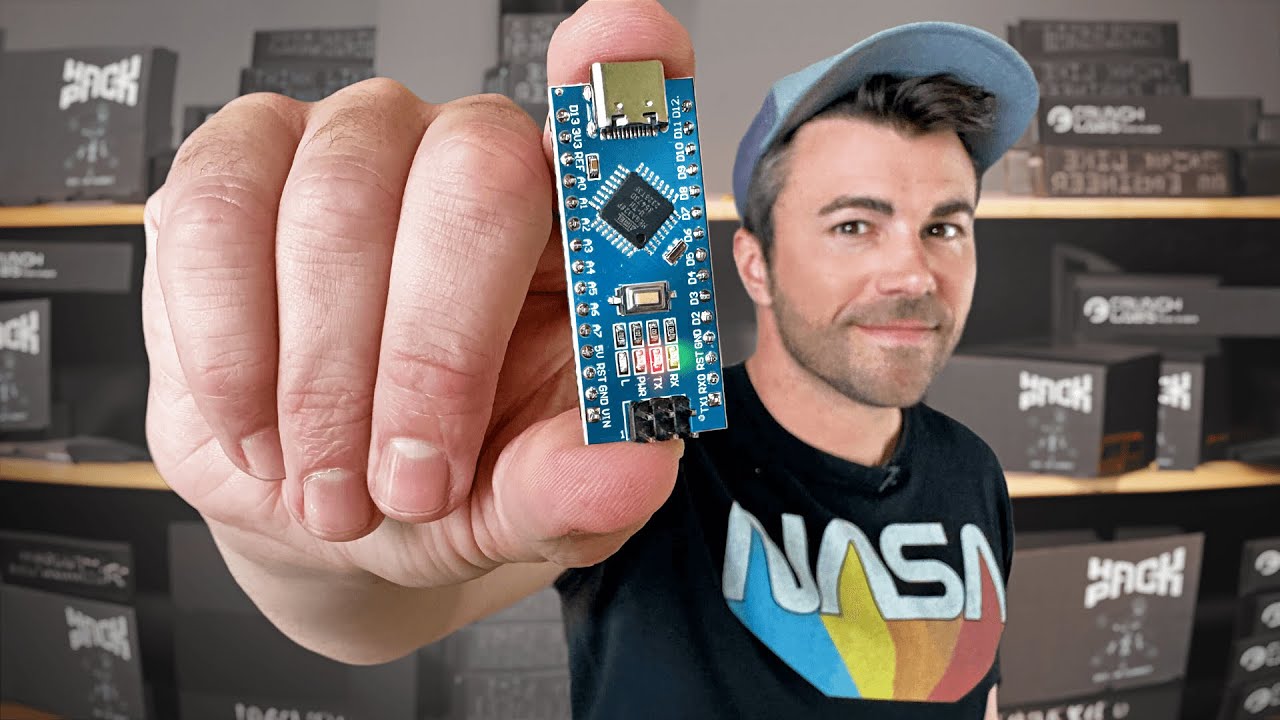
Learn How Hackers Delete Activity Logs and Remove Traces of Their Actions
Learn How Hackers Delete Activity Logs and Remove Traces of Their Actions This online course will teach you the techniques used by hackers to delete activity logs, erase digital footprints, and cover their tracks. Dive into the world of cybercrime with real-world examples and in-depth knowledge. Understand the methods used by attackers to erase traces and secure their operations, helping professionals to defend against them. Tags: Cybersecurity Hacking Techniques Digital Forensics Activity Log Deletion Cybercrime Prevention Security Training Ethical Hacking Data Protection Hackers Tools Cyber Attacks Online Course Digital Footprint Removal Hacking Awareness Online Security Course Privacy Protection Hashtags: #DeleteHackingActivity, #OnlineCourse, #Cybersecurity, #Hackers, #CyberCrime, #HackingTechniques, #DigitalForensics, #DataProtection, #SecurityTraining, #EthicalHacking, #ActivityLogDeletion, #CyberattackPrevention, #HackersTools, #EraseDigitalFootprints, #SecurityAwareness, #PrivacyProtection Releated Searches #how hackers remove logs, #hackers covering their tracks, #erase hacking activity, #delete hacking traces, #how to hide hacking activities, #log deletion methods by hackers, #how hackers hide their digital footprint, #cybercrime techniques, #how hackers erase their online presence, #cybersecurity hacks, #hackers erasing logs, #digital forensic analysis, #removal of online activity, #how to protect against hacking, #ethical hacking tools, #tracking hacker footprints, #preventing cybercrime, #logging activity removal, #how hackers delete evidence, #tools used by hackers to hide traces, #how hackers erase their tracks, #methods to remove hacking evidence, #how hackers clean activity logs, #covering up hacking activities, #security breach cover-up, #protect against hacker traces, #preventing data breaches, #hacking cleanup, #removing traces of cyber attacks, #cyber attack detection, #security breach prevention, #erasing digital footprint, #remove hacker traces from systems, #tracking and preventing hackers, #how hackers remove their identity, #cyber attack investigation, #hackers hiding data trails, #activity log monitoring, #how to secure systems from hackers, #best hacker tools to hide activity, #online security course for hackers, #prevent hacker detection, #erasing online traces, #how hackers remove logs on systems, #how to detect hacker activity, #methods of digital trace removal, #remove traces of cybercrime, #how hackers cover up cyber attacks, #learning ethical hacking, #cybersecurity learning, #prevention of online fraud, #track hacker activity, #online activity erasure techniques, #preventing digital privacy invasion, #how to hide from hackers, #cyber attack damage control, #protect your online identity from hackers, #how hackers use VPNs to hide activity, #hacker tools to erase logs, #how hackers break into systems and erase evidence, #staying anonymous online, #how to prevent online fraud, #data log cleanup from hackers, #computer security basics, #secure online privacy, #how hackers hack accounts and erase data, #steps to secure digital information, #protecting yourself from hackers, #safe from hackers guide, #erasing malicious activity, #prevent hacking data leaks, #how hackers disable logs, #hacker tools to cover their activity, #how hackers bypass tracking, #ways hackers remove system logs, #cybersecurity defense course, #digital footprint management, #hacker erasure tactics, #how to trace hacker activity, #keeping your data safe from hackers, #online fraud prevention tools, #how hackers track passwords, #online crime prevention methods, #erasing login activity, #protect online banking from hackers, #preventing account hacking, #computer forensic investigations, #identity protection from hackers, #how hackers get rid of logs, #learn cybersecurity from hackers, #hide online actions from hackers, #how hackers attack systems and remove evidence